Three individuals in the United Kingdom have admitted guilt in connection to the operation of otp[.]agency, a now-defunct online platform that facilitated the interception of one-time passcodes (OTPs) utilized by many websites for enhanced security.
The inception of OTP Agency dates back to November 2019 when it emerged as a tool for intercepting one-time passcodes crucial for logging into various online platforms. Cybercriminals who had already obtained the login credentials of unsuspecting victims could input the victim’s phone number and name into OTP Agency’s system. Consequently, OTP Agency would then initiate an automated phone call to the target, alerting them of unauthorized activities on their account. The call would prompt the victim to enter a one-time passcode generated by their mobile app, which was then redirected to the scammer’s user panel on the OTP Agency website.
Recently, the National Crime Agency (NCA) in the U.K. disclosed that three men have pleaded guilty to operating OTP Agency. The culprits include Callum Picari, 22, from Hornchurch, Essex; Vijayasidhurshan Vijayanathan, 21, from Aylesbury, Buckinghamshire; and Aza Siddeeque, 19, from Milton Keynes, Buckinghamshire.
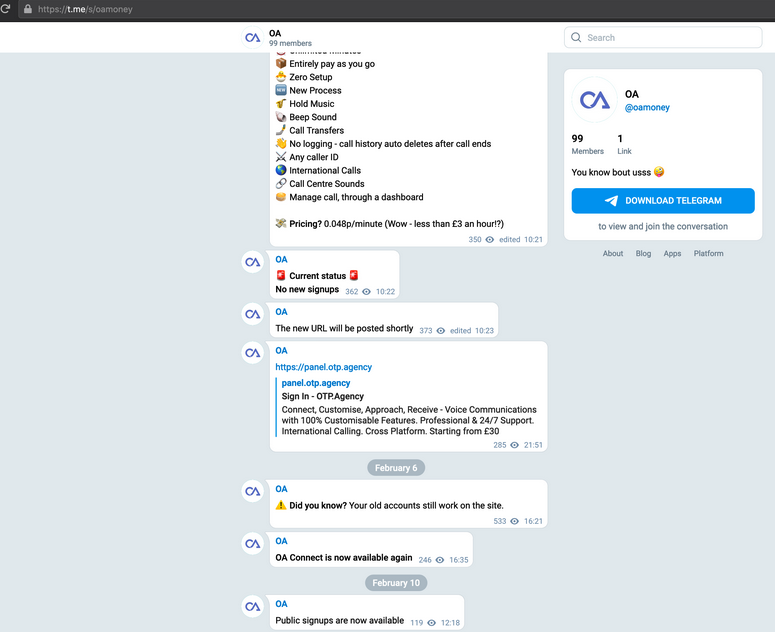
A previous report by KrebsOnSecurity shed light on OTP Agency in a story in February 2021, which led to arrests linked to another phishing-related service in the U.K. OTP Agency’s purported representative denied the allegations in the story, claiming the service was a legitimate anti-fraud measure. However, evidence from the service’s Telegram channel exposed the ulterior motive behind OTP Agency’s establishment – to facilitate account takeovers for its customers.
Following the exposure by KrebsOnSecurity, OTP Agency made a swift decision to shut down its website and notify users of its closure. However, the NCA revealed the frantic exchanges between Picari and Vijayanathan after the story’s publication, highlighting the incriminating chat logs and the subsequent decision to delete evidence of their fraudulent activities.
Despite the initial shutdown, OTP Agency resurfaced shortly after on a new Telegram channel, attempting to reassure existing customers that their login credentials and balances remained intact. However, this revival was short-lived, with the NCA reporting that the site was swiftly taken offline when the trio was apprehended. According to NCA investigators, over 12,500 individuals fell victim to OTP Agency users during its 18-month operation.
Picari was identified as the mastermind behind OTP Agency, responsible for its development and operation. His association with OTP Agency was unveiled in February 2020 on an English-language cybercrime forum, leading to the NCA commencing an investigation in June 2020.
Even though OTP Agency has ceased operations, several similar services that intercept OTPs still exist in the cybercriminal realm, including the long-standing service SMSRanger, as highlighted in a September 2021 report by KrebsOnSecurity.
In conclusion, the operation of OTP Agency serves as a stark reminder of the ongoing threat posed by online fraud and phishing scams. It is crucial for individuals to remain vigilant and refrain from sharing personal or financial information with unknown entities. Additionally, verifying the legitimacy of communication through official channels can help mitigate the risk of falling victim to such deceptive schemes.