Security Researchers Uncover Sophisticated Zero-Day Vulnerability Targeting Adobe Reader Users
Recent findings from security researchers at EXPMON have identified a highly sophisticated and unpatched zero-day vulnerability that is actively targeting Adobe Reader users. This concerning discovery was first made late last month as the exploit began appearing in real-world scenarios, suggesting an alarming level of threat to individuals and organizations that rely on this widely-used PDF software.
The vulnerability allows malicious actors to covertly steal local files, gather sensitive system information, and potentially execute remote code execution (RCE) attacks on compromised devices. These attacks can occur without requiring any user interaction beyond merely opening a malicious PDF document, highlighting the exploit’s dangerous efficiency.
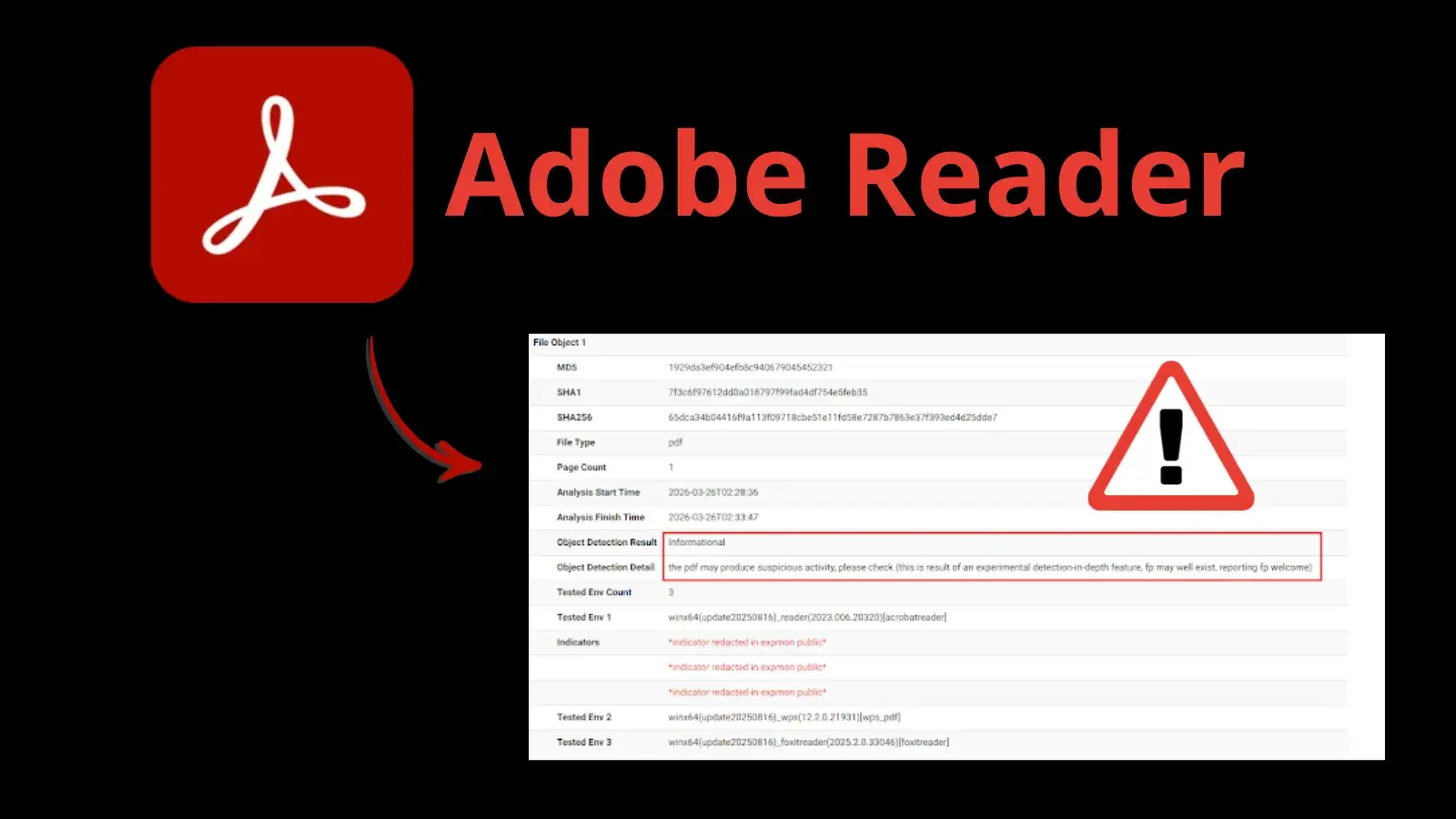
According to a threat intelligence report published by EXPMON founder Haifei Li, the malicious PDF, initially titled "yummy_adobe_exploit_uwu.pdf," has successfully circumvented various standard antivirus engines. In fact, on VirusTotal, it recorded a low detection rate of just 5 out of 64, underscoring the sophisticated nature of the exploit. Furthermore, it has been confirmed to operate effectively on the latest version of Adobe Reader at the time of reporting, which is version 26.00121367.
The strategy employed by this attack is particularly concerning because it leverages heavily obfuscated JavaScript embedded deeply within the PDF’s internal structure. The exploit has been found to utilize two privileged Acrobat application programming interfaces (APIs) for its operations. The first API, util.readFileIntoStream(), is tasked with reading arbitrary files stored on the compromised system, such as ntdll.dll, which is crucial for determining the operating system version. The second API, RSS.addFeed(), facilitates the exfiltration of this sensitive data to a remote server controlled by the attackers.
Alarmingly, the command server, which the attackers operate, is located at the IP address 169.40.2.68:45191. By using these methods, threat actors can effectively collect data on their victims, from system configurations to file paths. This initial reconnaissance serves as a means for the attackers to gauge whether a given machine is associated with a high-value target.
Once a target meets the attackers’ stringent criteria, the command server can then deliver encrypted secondary JavaScript payloads. Researchers have demonstrated in controlled environments that this connection can be used to execute remote code, enabling full exploitation capabilities that might lead to complete system control, and even sandbox escape attacks. During their real-world testing, however, the server withheld the final payload, likely due to the researchers’ test environment not conforming to the attackers’ specifications for target profiles.
EXPMON has taken the significant step of disclosing these findings to Adobe Security; however, as of now, there is no official patch available to address this vulnerability. This delay emphasizes the pressing need for heightened vigilance within the security community until a fix can be deployed.
To enhance security measures, network defenders are being urged to block the identified malicious IP address. Moreover, as threat actors are known to frequently rotate their infrastructure, security teams are encouraged to broaden their hunting strategies. This includes monitoring for unusual HTTP or HTTPS traffic that may contain "Adobe Synchronizer" in the User-Agent field.
As the threat landscape evolves, users are strongly advised to exercise extreme caution. It is recommended that individuals refrain from opening unsolicited PDF documents from unverified sources until Adobe releases a comprehensive security update.
With cyber threats becoming increasingly sophisticated, it is crucial for the community to stay informed and prepared. Organizations and individuals alike must be proactive in safeguarding their systems against such vulnerabilities, ensuring that they are not caught off guard by these evolving digital threats. A coordinated and informed response will be essential in navigating the complexities of cyber security in the era of digital reliance.