Recently, a shocking data breach involving Spoutible and its enumerable API has sent shockwaves through the infosec community. Amazed and curious about the reach of this breach, a file containing 207k scraped records was sent to an individual with a URL that led to revealing users’ information, including their hashed passwords, 2FA secrets, and password reset tokens. The breach has raised significant concerns regarding privacy and cybersecurity for users of the platform.
The Spoutible API breach was discovered when a file containing scraped records of user information was sent to an individual, leading to the discovery of a URL that returned sensitive user data, including hashed passwords, 2FA secrets, and password reset tokens. This incident raised significant concerns over the platform’s security and the privacy of its users.
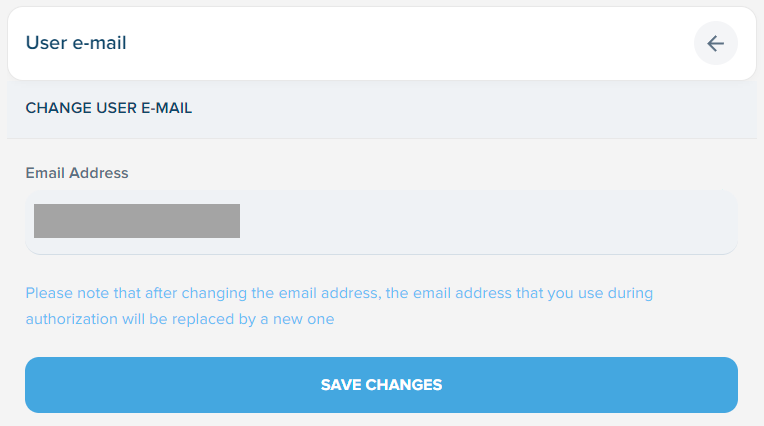
The API enabled the retrieval of the bcrypt hash of any user’s password, a practice that has been heavily criticized by cybersecurity experts. While bcrypt is a strong hashing algorithm, it is not entirely immune to cracking, especially in cases where weak passwords are allowed. Additionally, the API allowed for the easy creation of passwords without any strength checks, further exposing users to security risks.
Furthermore, the API also exposed users’ 2FA secrets, rendering the two-factor authentication process useless. Additionally, the password reset tokens were publicly exposed, potentially allowing unauthorized access to user accounts. The lack of notification for changed passwords and the inability to invalidate existing sessions further compounded the problems faced by affected Spoutible users.
The vulnerability of the API was also highlighted by the ease with which it was discovered. The Spoutible platform’s feature, Pods, allowed for the easy display of users’ information, adding to the concerns of the breach’s extent.
As the news of the Spoutible data breach continues to circulate, cybersecurity professionals are urging users to change their passwords and enable 2FA if they haven’t already. The incident serves as a stark reminder of the importance of robust security practices and the need for platforms to prioritize user privacy and data protection.
In response to the breach, Spoutible has stated that they are investigating the matter and taking steps to address the security vulnerabilities identified. The company has assured users that their team is working diligently to enhance the platform’s security measures and prevent similar breaches from occurring in the future.
Ultimately, the Spoutible data breach serves as a wake-up call for both users and platform operators, underscoring the critical need for robust cybersecurity measures and proactive security practices in an increasingly digital and interconnected world. The incident highlights the potential risks and consequences of inadequate security protocols and the importance of prioritizing user privacy and data protection in today’s digital landscape.