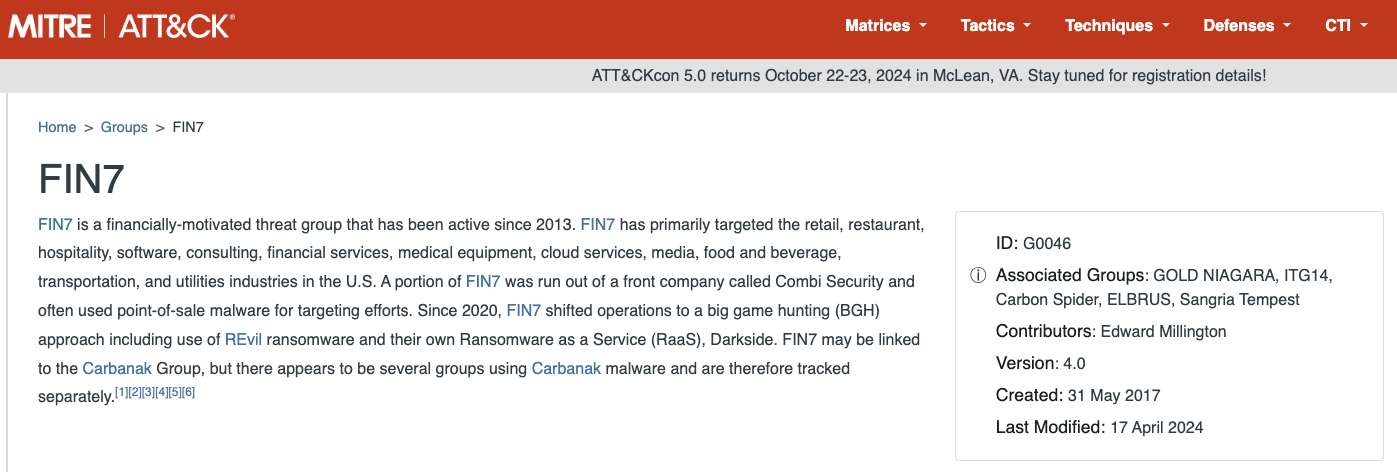
The notorious Russia-based cybercrime group known as “Fin7,” which was declared dead by U.S. authorities last year, has resurfaced in 2024 with a vengeance. Operating in collaboration with Stark Industries Solutions, a prominent hosting provider with ties to Russia, Fin7 has launched a new wave of cyberattacks targeting organizations worldwide.
In a bold move in May 2023, the U.S. attorney for Washington state announced the demise of Fin7 after securing convictions against key members of the group. However, recent reports from security experts suggest that Fin7 has been resurrected and is now actively engaging in phishing and malware attacks to infiltrate victim organizations.
Security firm Silent Push has uncovered Fin7’s extensive cybercrime infrastructure, consisting of over 4,000 hosts utilizing various tactics such as typosquatting, booby-trapped ads, and spearphishing domains. These domains mimic popular brands like American Express, Google, Microsoft, and Netflix, among others, to deceive unsuspecting victims.
According to Zach Edwards, a senior threat analyst at Silent Push, Fin7 employs a strategy of creating innocent-looking websites to establish a positive reputation for their domains before launching brand-specific phishing campaigns. This tactic allows them to evade detection and effectively target individuals seeking legitimate software tools.
One of Fin7’s latest tactics involves utilizing sponsored Google ads to distribute malware through fake browser extensions. Security firms like eSentire and Malwarebytes have observed these malicious campaigns and warned users to be cautious when encountering pop-ups prompting them to download suspicious software.
Silent Push’s investigation also revealed Fin7’s association with Stark Industries Solutions, a hosting provider implicated in cyberattacks against Ukraine linked to Russian military and intelligence agencies. The discovery of Fin7’s extensive network of domains hosted by Stark Industries Solutions indicates a significant resurgence in the group’s malicious activities.
In addition to hosting phishing sites, Fin7 has been known to create fake cybersecurity companies to recruit security experts for ransomware attacks. The emergence of new domains like cybercloudsec[.]com indicates that Fin7 is actively seeking partnerships under the guise of providing IT, cybersecurity, and cloud solutions.
As the Summer Olympics approach, Fin7 has shifted its focus to target tourists visiting France, particularly those seeking tickets to attractions like the Louvre. This adaptation to current events showcases Fin7’s agility in exploiting trending topics to lure unsuspecting victims.
Overall, the resurgence of Fin7 underscores the persistent threat posed by cybercriminal groups and highlights the need for increased vigilance and cybersecurity measures. Law enforcement agencies and cybersecurity experts are urged to monitor Fin7’s activities closely and take proactive measures to combat their malicious campaigns.
For more information on Fin7 and Stark Industries Solutions, readers can refer to additional resources provided in the article.