In the world of cybersecurity, the battle between blue teams and red teams is ongoing. While blue teams focus on defending organizations against potential threats, red teams take on the role of attackers, simulating real-world attacks to identify weaknesses in security systems. Both sides work together to enhance overall security measures and protect organizations from malicious actors.
Recently, a closer look was taken at some open-source tools that blue teams utilize for defense, as well as gadgets that could potentially cause security issues if misused. Now, the spotlight shifts to five cutting-edge tools that hobbyist hardware hackers, red teamers, and ethical hackers may leverage for skill development or professional purposes.
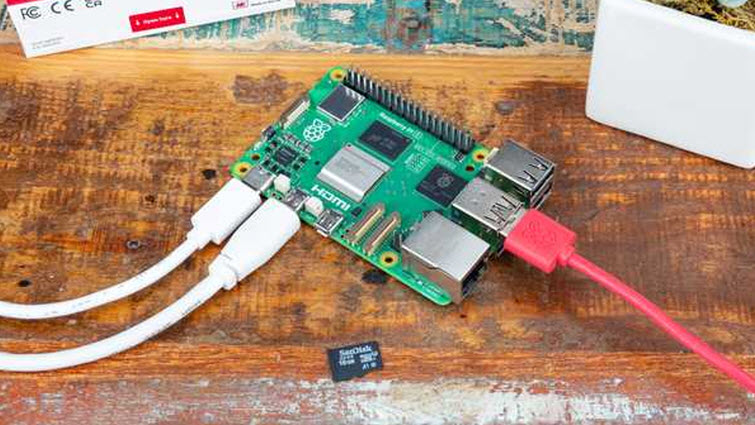
1. Raspberry Pi 5:
The Raspberry Pi has emerged as a popular tool within the cybersecurity community due to its versatility and affordability. This single-board computer can be equipped with various penetration testing tools, allowing users to analyze network traffic, conduct security tests, and assess IoT device vulnerabilities. Operating systems like Kali Linux are specifically designed for penetration testing and come pre-loaded with essential tools.
Additionally, specific projects like FruityWifi and PwnPi leverage the Raspberry Pi platform to enhance wireless network auditing capabilities and simplify Debian Wheezy for penetration testing purposes.
2. HackRF One:
The HackRF One serves as a valuable tool for exploring radio frequency signals, enabling users to transmit and receive signals across a broad spectrum. This software-defined radio device can be used for analyzing various wireless communication protocols, making it an essential gadget for security professionals and RF enthusiasts. Its portability and robust design allow for on-the-go fieldwork to test network vulnerabilities and troubleshoot signal issues.
3. WiFi Pineapple:
The WiFi Pineapple may require a bit more pocket space, but its impact on wireless network security testing is significant. This gadget simulates a legitimate access point to attract unsuspecting users, allowing for the identification of vulnerabilities and security gaps. The Pineapple OS, a custom operating system optimized for wireless penetration testing, equips the device with essential tools for assessing network security and developing better security policies.
4. Deauther Watch:
Taking the form of a wearable gadget, the Deauther Watch is capable of executing Wi-Fi deauthentication attacks to disrupt connections between devices and Wi-Fi routers. This device can also perform Wi-Fi scanning and packet capturing, making it an essential tool for detecting vulnerabilities and monitoring network activity.
5. Ubertooth One:
Designed for monitoring Bluetooth communications and analyzing Bluetooth packets, the Ubertooth One is a powerful tool for testing Bluetooth-enabled IoT devices. Its open-source platform supports various security testing scenarios, including sniffing for sensitive information exchanged over Bluetooth connections. With capabilities that extend beyond conventional Bluetooth adapters, the Ubertooth One is adaptable for specific security testing needs.
While these gadgets offer valuable capabilities for security professionals and ethical hackers, it is crucial to emphasize ethical considerations. The use of these tools should be limited to authorized environments and purposes, such as controlled testing or educational activities. Unauthorized use of these devices for malicious purposes can lead to legal consequences, underscoring the importance of implementing comprehensive security measures, policies, and user education within organizations to safeguard against potential threats.