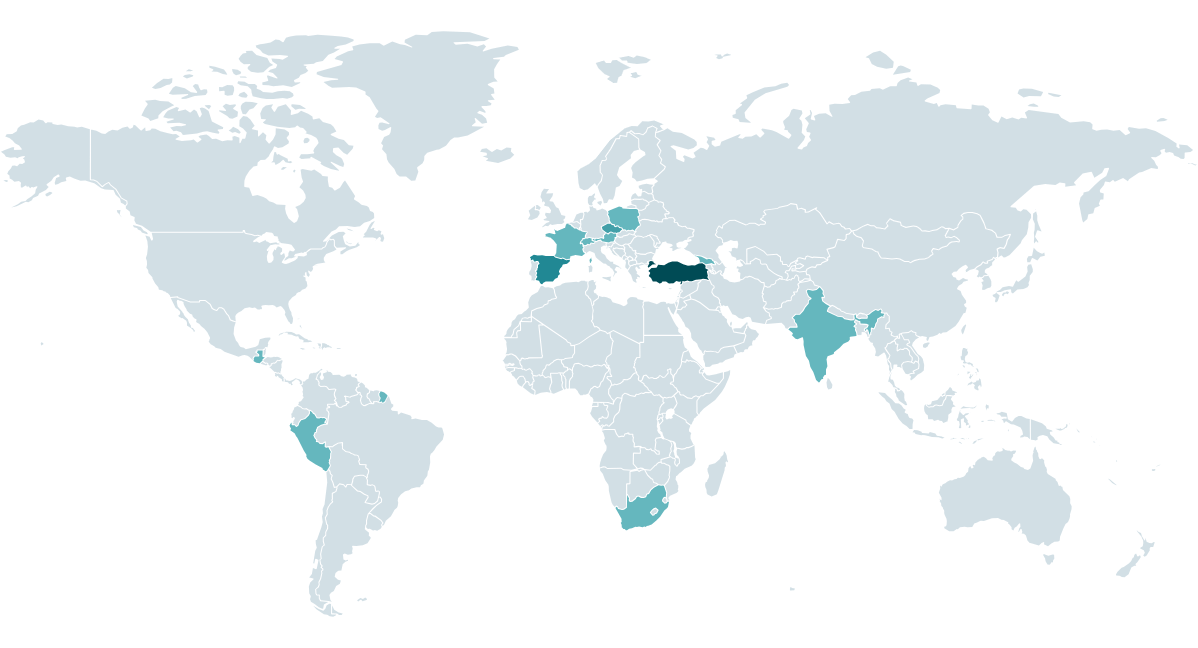
In a recent blog post published by ESET researchers, the activities of the CosmicBeetle threat actor were extensively documented. The researchers highlighted the emergence of the new ScRansom ransomware and its connection to other well-established ransomware gangs. CosmicBeetle has been actively deploying ScRansom to small and medium-sized businesses (SMBs) across different regions worldwide. Despite not being considered a top-tier threat actor, CosmicBeetle has been able to compromise a range of interesting targets.
One significant development within CosmicBeetle’s operations is the replacement of its previously used ransomware, Scarab, with the new and continually improved ScRansom. The threat actor has also been observed utilizing the leaked LockBit builder and attempting to exploit LockBit’s reputation by imitating this notorious ransomware gang in ransom notes and on leak sites. Furthermore, there are strong indications that CosmicBeetle may be an affiliate of RansomHub, a relatively new ransomware gang that has been increasingly active since March 2024.
The research conducted by ESET delves into the activities of CosmicBeetle over the past year, shedding light on its tactics, techniques, and procedures. The analysis also provides valuable insights into the ScRansom ransomware. Despite its relatively unsophisticated nature, ScRansom has still managed to cause considerable harm to its victims. Victims who opt to pay the ransom should exercise caution, as some encrypted files may be irreversibly lost during the decryption process.
One notable strategy employed by CosmicBeetle is the attempt to piggyback off the notoriety of the LockBit ransomware gang. By impersonating LockBit and leveraging its brand, CosmicBeetle sought to increase the chances of receiving ransom payments from victims. This tactic underscores the threat actor’s willingness to exploit established ransomware affiliations for its gain.
Moreover, the researchers’ analysis points to a potential link between CosmicBeetle and RansomHub, another emerging ransomware-as-a-service gang. The observation of ScRansom and RansomHub payloads being deployed on the same machine within a short timeframe indicates a possible affiliation between CosmicBeetle and RansomHub. This connection could have significant implications for the cyber threat landscape and ransomware ecosystem.
In terms of technical analysis, ESET researchers found that CosmicBeetle predominantly employs Delphi-based tools in its operations, including ScRansom. The ransomware utilizes a complex encryption scheme, which has evolved over time to make decryption more challenging. Victims of ScRansom are required to navigate a cumbersome decryption process, involving multiple decryption keys and potential data loss. This approach by CosmicBeetle contrasts with the streamlined decryption methods commonly employed by more established ransomware groups.
Overall, the detailed research conducted by ESET sheds light on the evolving tactics of the CosmicBeetle threat actor and its connections to other ransomware gangs. By providing valuable insights into the workings of ScRansom and the broader modus operandi of CosmicBeetle, the researchers aim to enhance understanding of the evolving cyber threat landscape and empower organizations to better defend against such malicious actors.