Law enforcement agencies from Thailand, Singapore, and cybersecurity firm Group-IB have successfully collaborated to apprehend a notorious hacker involved in more than 90 data breaches globally. The hacker, known by various online aliases like GHOSTR, ALTDOS, DESORDEN, and 0mid16B, has been accused of stealing and selling over 13 terabytes of sensitive information, including government agency records, on dark web platforms. Additionally, the hacker was an active member of Breach Forums, a notorious cybercrime and data breach platform.
The hacker, operational since 2020, initially targeted organizations in Asia-Pacific countries such as Thailand, Singapore, Malaysia, Pakistan, and India, before expanding their activities to Europe, North America, and the Middle East. The victims of the hacker span multiple industries, including healthcare, finance, e-commerce, and logistics.
The modus operandi of the hacker involved pressuring companies by threatening to leak stolen data if ransom demands were not met. Subsequently, they began selling databases on dark web forums, gaining a reputation for providing high-quality data and charging premium prices. In some instances, they even resorted to directly contacting customers to coerce companies into compliance.
According to Group-IB’s press release, the hacker exploited common vulnerabilities to infiltrate systems, employing tools like sqlmap for SQL injections and targeting poorly secured Remote Desktop Protocol (RDP) servers. They utilized a modified version of CobaltStrike, a penetration-testing tool, to maintain control over compromised networks and store extracted data on cloud servers for extortion purposes.
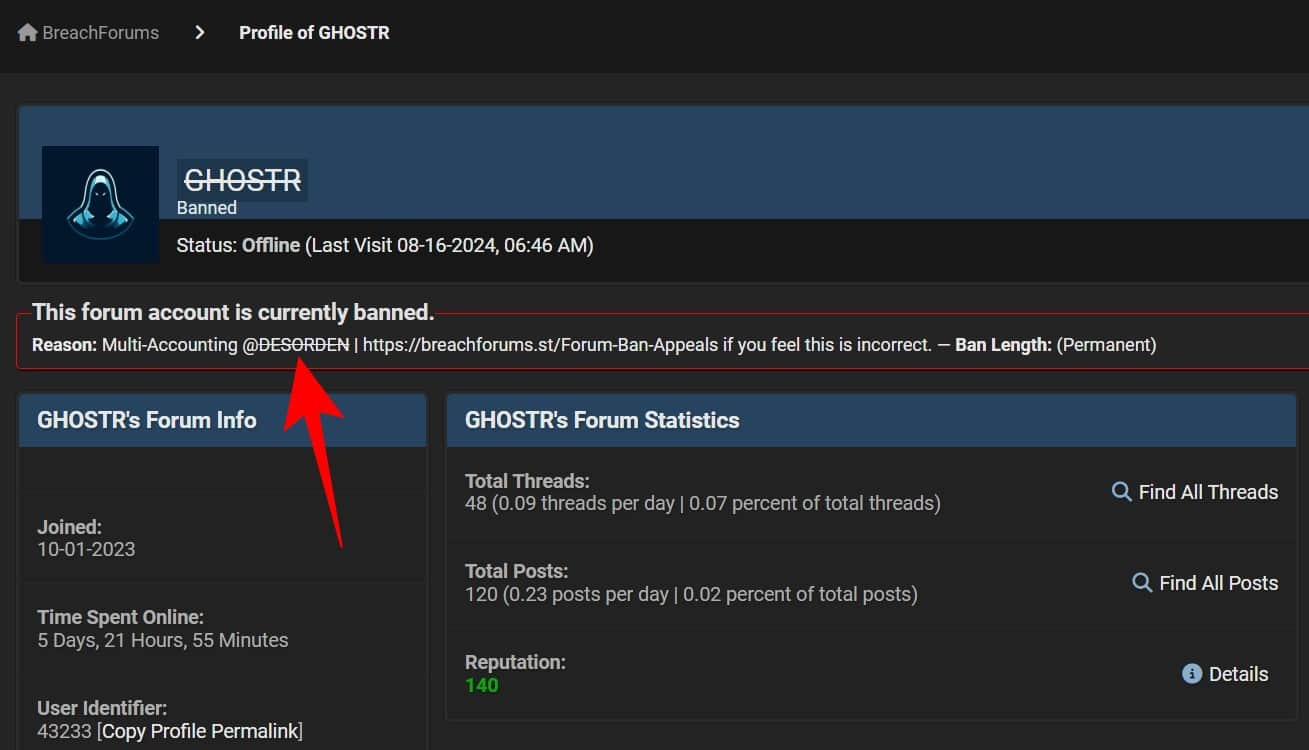
One of the significant challenges faced by investigators was the hacker’s frequent change of aliases and tactics. Group-IB’s analysts managed to link the different identities by analyzing writing styles, post formats, and target preferences across dark web forums. Despite facing bans on forums for fraudulent activities, the hacker continued their operations under new identities until law enforcement authorities were able to trace their real-world identity.
During the hacker’s arrest, Thai authorities seized several laptops, electronic devices, and luxury items purchased using the profits from data sales. Group-IB’s involvement in tracking the hacker’s activities across various aliases showcases the importance of behavioral patterns and technical clues in identifying and apprehending persistent cybercriminals. This successful operation is reminiscent of the case of the Brazilian hacker USDoD, who was captured after his real identity was exposed by CrowdStrike, leading to his subsequent arrest.