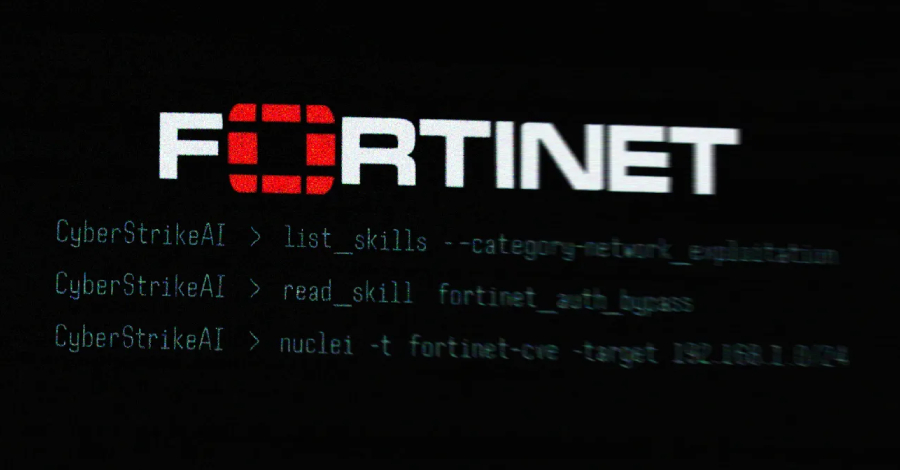
The increasing threat posed by cyberattacks has recently gained attention due to the revelation of an AI-assisted campaign aimed at exploiting Fortinet FortiGate appliances. This operation was orchestrated by a threat actor who utilized an open-source platform known as CyberStrikeAI to execute their attacks effectively. The findings emerged from a detailed analysis conducted by Team Cymru, which investigated the suspicious IP address (212.11.64[.]250) linked to the intrusions. The team traced these activities back to a suspected Russian-speaking group actively engaging in automated scans targeting vulnerable FortiGate devices.
CyberStrikeAI is a sophisticated offensive security tool developed by an individual known only by the online alias Ed1s0nZ. The tool is characterized as an open-source initiative that integrates over 100 security resources, enabling users to discover vulnerabilities, analyze attack chains, retrieve valuable knowledge, and visualize results. The developer is believed to have connections to the Chinese government, raising concerns about potential state-sponsored hacking activities.
The campaign came to light in the previous month when Amazon Threat Intelligence reported that an unidentified attacker was systematically targeting FortiGate devices. Utilizing advanced generative AI services such as Anthropic Claude and DeepSeek, the attacker was able to compromise more than 600 appliances across 55 countries. This level of coordinated attack signifies a worrying trend in the digital landscape, with AI technologies being weaponized for malicious purposes.
According to Team Cymru’s research, the usage of CyberStrikeAI was traced across 21 distinct IP addresses between January 20 and February 26, 2026. Notably, many of these servers were located in China, Singapore, and Hong Kong, with additional hosts found in the United States, Japan, and Switzerland. The geographical distribution of these servers further underscores the international dimension of the cyber threat landscape, indicating that this issue transcends national borders and requires concerted global cooperation to effectively combat it.
Beyond CyberStrikeAI, Ed1s0nZ has developed a range of other tools that underline a clear interest in cybersecurity exploitation and the jailbreaking of AI models. These include various applications such as the watermark-tool, designed to add invisible digital identifiers to documents; banana_blackmail, a ransomware solution; and PrivHunterAI, a tool that detects privilege escalation vulnerabilities. Another noteworthy application is ChatGPTJailbreak, which provides instructions on manipulating OpenAI’s ChatGPT into bypassing its built-in safety mechanisms.
Further scrutiny into Ed1s0nZ’s online activities highlights interactions with organizations potentially aligned with state-sponsored cyber operations in China. For instance, Ed1s0nZ has been linked to Knownsec 404, a Chinese security company that suffered a significant data breach last year. This incident exposed over 12,000 internal documents, showcasing not only the company’s employee data but also sensitive information related to governmental clientele and ongoing cyber operations targeting other nations. Such leaks raise alarm bells regarding the extent to which private sector firms may support or collaborate with state actors in the realm of cyber espionage.
DomainTools, in a recent analysis, characterized Knownsec as more than a mere cybersecurity vendor, suggesting that it functions as a “state-aligned cyber contractor.” The report claims that Knownsec has the capacity to assist Chinese national security and military objectives, further complicating the cyber landscape. The company’s operations extend beyond traditional cybersecurity services, allegedly possessing capabilities that allow for global reconnaissance and strategic exploitation of vulnerabilities in critical infrastructure across various nations.
In addition to his development work, Ed1s0nZ has made alterations to repository files, such as removing accolades referencing his acknowledgment by the China National Vulnerability Database (CNNVD). This modification appears to be an attempt to disguise state affiliations, likely to ensure the operational viability of CyberStrikeAI amidst growing scrutiny. Analysts have observed a trend where Chinese authorities maintain two vulnerability databases, CNNVD and the Chinese National Vulnerability Database (CNVD), with the former being managed by the Ministry of State Security. This division highlights the complexity involved in navigating vulnerabilities, with implications on the speed of disclosure based on the potential impact on national security.
Researchers fear that the increased adoption of tools like CyberStrikeAI could represent a turning point in the evolution of cyber warfare, as malicious actors increasingly leverage AI for offensive strategies. As these technologies become more accessible, the cyber threat landscape may undergo significant transformations, necessitating a robust response from international cybersecurity agencies and governments to mitigate the ramifications of such sophisticated attacks. The emergence of AI-enhanced tools raises pressing questions about the future of cybersecurity, the nature of state-sponsored operations, and the necessary steps to build an effective defense against an ever-evolving array of cyber threats.