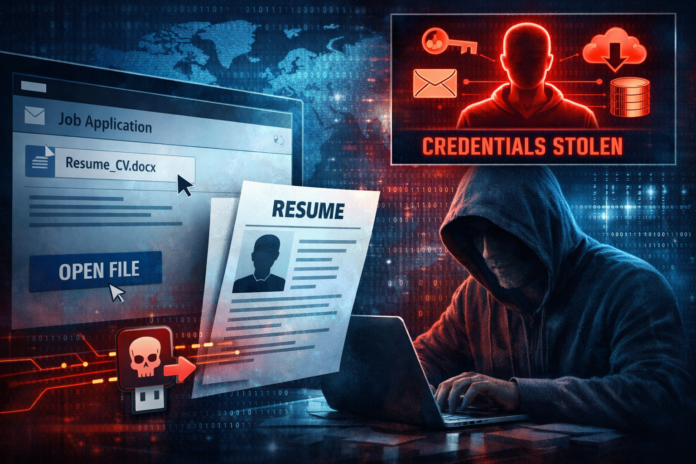
A new cyberattack campaign is turning a routine business process into a serious security risk. Threat actors are now distributing fake job applications containing malicious files, allowing them to infiltrate corporate systems and steal sensitive data.
The campaign, identified as FAUX#ELEVATE, targets organizations by sending emails that appear to come from legitimate job candidates. Attached to these emails are resumes that look normal but actually contain hidden malicious scripts. Once opened, the file quietly executes in the background without raising immediate suspicion.
From that point, the attack progresses rapidly. Within seconds, the malware connects to external infrastructure to download additional components and begin extracting sensitive information from the infected system. This includes stored credentials, browser data, and other valuable corporate information. In some cases, the attackers also deploy cryptocurrency mining software, although the primary objective appears to be long-term access through stolen credentials.
What makes this campaign particularly effective is its ability to blend into everyday workflows. HR teams and recruiters regularly receive resumes from unknown senders, making these emails far less suspicious than traditional phishing attempts. As a result, users are more likely to open the attachments without hesitation.
The malware also includes techniques designed to avoid detection. It may check whether the infected machine is part of a corporate environment before continuing its execution, ensuring that only high-value targets are affected. Additionally, the use of legitimate services such as cloud hosting platforms helps the attackers hide their activity within normal network traffic.
The impact of such an attack can extend well beyond a single compromised device. Once credentials are stolen, attackers can move deeper into the organization, access internal systems, and potentially prepare for larger attacks such as data exfiltration or ransomware deployment.
This campaign highlights how cyber threats continue to evolve by exploiting trusted processes rather than obvious vulnerabilities. As attackers become more creative, organizations must place greater emphasis on user awareness, careful handling of email attachments, and monitoring for unusual system behavior.
In a landscape where even a resume can be weaponized, vigilance at every level has become essential.