PlayStation hacker known as Shuffle2 has recently unveiled his latest presentation at SAS2024, where he discussed the decryption of the PlayStation 5’s EMC/EAP chips. The presentation not only showcased the slides used during the event but also introduced a new set of tools called ps5-uart that exploit the aforementioned chips on the PS5.
While the ps5-uart tools may not be immediately beneficial to regular users looking to experiment with their PS5 consoles, it has garnered the attention of hackers within the gaming community who are eager to explore the potential exploits and interact with other systems within the PS5 using the newly discovered vulnerabilities.
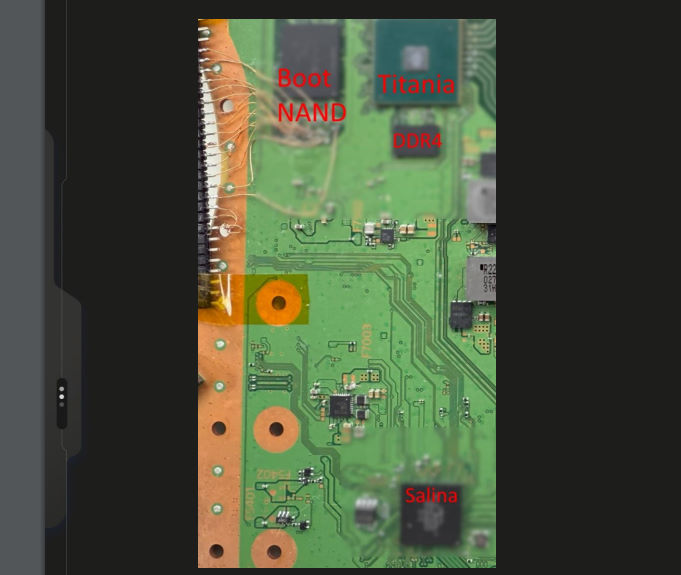
One of the key focuses of Shuffle2’s presentation was on the Salina and Titania exploits, which were used to exploit the power and clock management chip (Salina) and the media device communication chip (Titania) on the PS5 board, respectively. For Salina, a buffer overflow was identified through its UART communication protocol, while for Titania, a stack buffer overflow was discovered that allowed for the exploitation of the system.
In the case of Salina, the chip responsible for power and clock management on the PS5 board, an exploit was found through an overflow in its UART communication. This vulnerability allowed hackers to gain access to the chip’s functions and potentially control aspects related to power and clocking within the console.
On the other hand, Titania, which handles communication with various media devices on the PS5 board such as the SSD, was also found to have a stack buffer overflow exploit. This exploit provided an entry point for hackers to manipulate communication with media devices and potentially impact system functionality related to downloads and other media-related operations.
For those interested in delving deeper into the details of Shuffle2’s presentation and the associated exploits, the slides can be accessed online. Additionally, the ps5-uart tools, which implement the exploits discovered, are available for download on the project’s GitHub page. The tools enable users to interact with the chips through UART communication, providing a platform for further exploration and experimentation.
The ps5-uart tools offer a range of commands that allow users to reset the syscon (EMC) chip, exploit the EMC and EFC chips, and interact with specific components of the PS5 system. These tools provide a glimpse into the potential capabilities that hackers and developers may unlock through further research and experimentation with the PlayStation 5’s hardware.
In conclusion, Shuffle2’s presentation and the release of the ps5-uart tools have opened up new possibilities for the hacking and modding community within the PlayStation ecosystem. As hackers continue to explore and exploit vulnerabilities in gaming hardware, it will be interesting to see how these discoveries shape the future of PlayStation console modifications and customizations.