A recent investigation has brought to light a significant web skimming campaign that has impacted at least 17 websites, including the UK site of electronics giant Casio. Researchers have uncovered these infections, which are believed to have originated from vulnerabilities in Magento or similar e-commerce platforms. Efforts are underway to inform all affected parties of the issue.
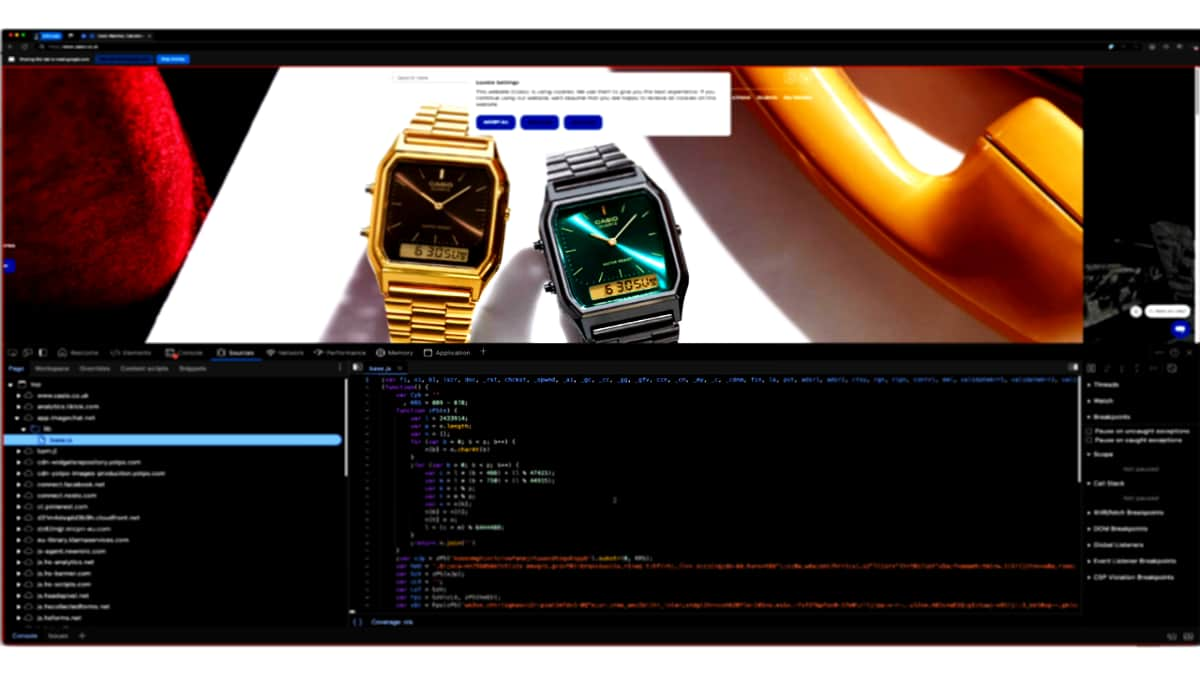
The web skimmer infection targeting the UK website of Casio and 16 other victims was detected on January 28. According to a blog post by researchers Pedro Fortuna, David Alves, and Pedro Marrucho, the skimmer utilized a double-entry web skimming attack. Victims were found to have loaded a script from the same Russian hosting provider, indicating the possible use of a web skimming toolkit.
Further investigation revealed that the skimmer infections likely exploited vulnerabilities in Magento webstores. Some hosting domains traced back for up to 16 years, suggesting that attackers took advantage of the reputation of older, potentially inactive domains.
Unlike traditional skimmers that focus on checkout pages, this particular skimmer targeted the cart page. It intercepted the checkout button click and presented users with a fake multi-step payment form in a pop-up window. This form collected sensitive information such as names, billing addresses, contact details, and credit card information.
After submitting the fake form, users received an error message and were redirected to the legitimate checkout page, where they were prompted to enter their payment details again – a tactic known as double-entry skimming. The skimmer also featured a flaw that spared users who clicked “buy now” instead of “add to basket.”
The attack on Casio UK involved a two-stage skimmer, with an initial loader disguising itself as a typical third-party script before injecting a more complex, obfuscated second-stage skimmer. This second-stage skimmer employed various techniques to evade detection, including custom encoding and XOR-based string concealment.
Data stolen by the skimmer was encrypted using AES-256-CBC before being sent out. Researchers were able to decrypt the data using the key and initialization vector included in the exfiltration request. The exfiltrated information encompassed a wide array of sensitive data, including billing addresses, contact details, and complete credit card information.
The Casio UK infection, which occurred between January 14th and 24th, was swiftly addressed within 24 hours of the company being notified. Research indicated that Casio UK’s Content Security Policy (CSP) was found to be ineffective in preventing the attack, primarily due to its report-only mode configuration and inadequate reporting mechanisms.
In conclusion, the incident involving casio.co.uk underscores the challenges associated with managing Content Security Policy (CSP). While a relatively straightforward standard, CSP can be complex to implement effectively. Mistakes in configuration may lead companies to opt for a report-only approach over blocking, potentially diminishing the security benefits provided by CSP. Researchers emphasized the importance of robust CSP implementation to mitigate such attacks in the future.