New Cybersecurity Threat: Bad Actors Pose as IT Support
In the ever-evolving landscape of cybersecurity, threat hunters have uncovered a concerning new campaign in which malicious actors disguise themselves as fake IT support personnel to proliferate the Havoc command-and-control (C2) framework. This deceptive strategy aims to facilitate data exfiltration or initiate ransomware attacks.
The campaign, disclosed by Huntress in a recent report, has been identified across five partner organizations. The sophisticated operation begins with a barrage of spam emails designed as lures that lead victims to unwittingly engage with the cybercriminals. Following this, a phone call from a purported IT desk reinforces the scam, activating a multi-layered delivery pipeline for malware. This clever approach not only enhances the chances of success but also highlights a worrying trend in cybercrime tactics.
In a chilling example from one organization, researchers Michael Tigges, Anna Pham, and Bryan Masters documented that the adversaries transitioned from their initial access point to infecting an additional nine endpoints within just eleven hours. This rapid lateral movement, coupled with a mix of custom Havoc Demon payloads and legitimate remote monitoring and management (RMM) tools employed for persistence, strongly indicates that the attackers were aiming for either data exfiltration, ransomware deployment, or possibly both.
Importantly, this approach aligns with broader attacks previously linked to the Black Basta ransomware group, which had garnered attention for its sophisticated social engineering tactics employing email bombing and phishing attacks via platforms like Microsoft Teams. Although this particular group has seemingly remained silent following the leak of its internal communications last year, the methodology they had adopted appears to have been emulated by other cybercriminals.
There are two prevailing theories about this situation. One suggests that former members of Black Basta have migrated to different ransomware operations, repurposing their skills to launch fresh attacks. The alternative theory posits that rival groups have assimilated similar strategies to gain initial access through social engineering.
The attack sequence begins with an extensive spam campaign aimed at inundating the inboxes of a target audience. Once the victim engages, the impersonators, feigning as IT support, often persuade individuals to grant them remote access to their systems. They accomplish this either through a Quick Assist session or by persuading users to install popular remote access tools such as AnyDesk.
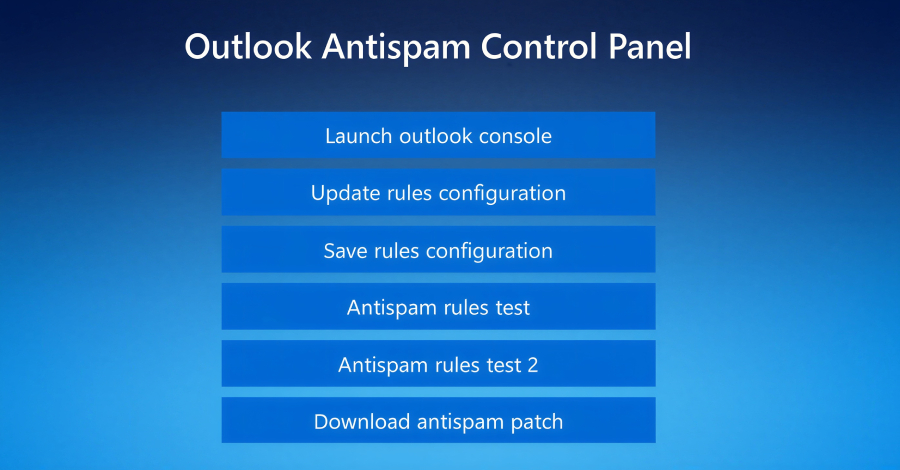
With remote access established, the attackers swiftly direct victims to a counterfeit webpage impersonating Microsoft. This fake landing page, hosted on Amazon Web Services (AWS), prompts the victim to enter their email address to supposedly access an “update” for Outlook’s anti-spam rules. Upon clicking the option to "Update rules configuration," the user unwittingly initiates a script designed to harvest their credentials.
This scheme serves a dual purpose: it enables the attackers to collect sensitive information needed to access more secure areas of the victim’s systems while simultaneously providing a veneer of authenticity to the interaction, convincing victims they are partaking in a legitimate process.
The next step typically involves the download of the fictitious anti-spam patch, which leads to the execution of a legitimate binary file such as “ADNotificationManager.exe.” This action is crafted to sideload a malicious Dynamic Link Library (DLL). This DLL is instrumental for evading detection and executing the Havoc shellcode payload through the installation of the Demon agent.
At least one identified DLL, named “vcruntime140_1.dll,” employs sophisticated tactics to elude conventional security measures. These tactics include control flow obfuscation, timing-based delay loops, and methods designed to bypass endpoint detection and response (EDR) solutions, effectively allowing the malware to operate unnoticed.
The researchers documented that once the Havoc Demon payload was successfully deployed on the compromised systems, the attackers commenced their lateral movement throughout the victim’s network. While the initial social engineering tactics and the sophisticated malware delivery were notably intricate, the subsequent steps taken to sustain their access were comparatively straightforward.
This phase typically includes establishing scheduled tasks that ensure the Havoc Demon payload is executed upon system reboots, thereby granting the attackers continuous but subtle control over the infected endpoints. Some instances involved the cybercriminals employing legitimate RMM tools, like Level RMM and XEOX, on compromised hosts. This diverse tactic serves to enhance their persistence and evade detection.
The critical takeaways from these incidents reveal several alarming trends. Notably, the readiness of threat actors to impersonate IT staff and reach out via personal phone numbers marks a significant escalation in sophistication. Defense evasion techniques once reserved for advanced state-sponsored attacks or major corporations are now increasingly being adopted by various malicious groups.
Additionally, the rapid pace with which these attacks transition from initial compromise to full network infiltration is alarming. The multitude of tactics employed to maintain persistent access illustrates the need for organizations to bolster their defenses and remain vigilant against such sophisticated schemes.
Ultimately, what begins as a seemingly innocuous phone call from “IT support” can culminate in a fully orchestrated network breach, complete with the deployment of modified Havoc Demons and legitimate RMM tools repurposed for ulterior motives. As researchers at Huntress concluded, this campaign exemplifies modern adversaries layering sophistication at every stage—from social engineering to secure access, to employing DLL sideloading for stealth, all while ensuring diversified mechanisms for persistence during their operations.