A new cybersecurity campaign has emerged, employing the ClickFix social engineering tactic to disseminate a previously undocumented malware loader known as DeepLoad. This tactic has raised alarms among cybersecurity experts as it presents a sophisticated method for cybercriminals to execute their malicious intents.
According to researchers from ReliaQuest, Thassanai McCabe and Andrew Currie, DeepLoad likely utilizes AI-assisted obfuscation and process injection techniques to evade static scanning measures employed by antivirus software. This initial phase of the attack focuses on credential theft, capturing passwords and session data almost immediately, even if the primary loader is being blocked by defenses.
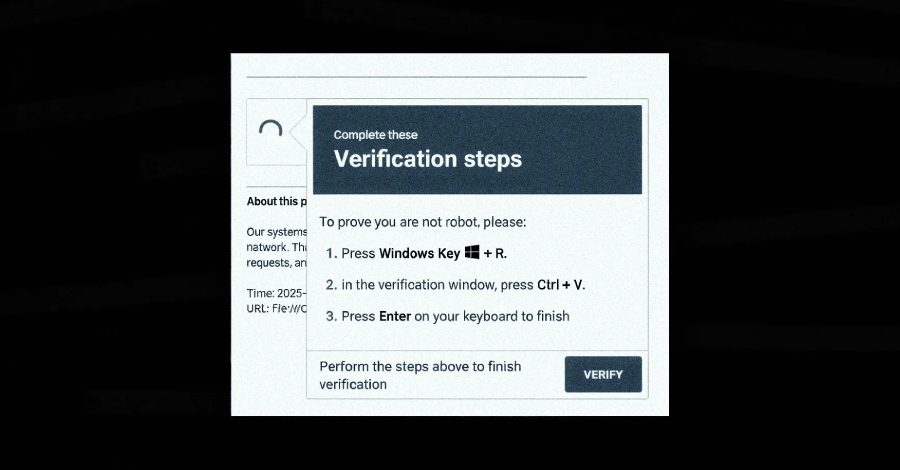
The attack commences with a ClickFix lure that deceives users into executing PowerShell commands. Users are tricked into believing they are resolving a non-existent system issue by copying and pasting a command into the Windows Run dialog. The operation subsequently calls upon “mshta.exe,” a legitimate Windows utility, to download and execute an obfuscated PowerShell loader designed to conceal its true purpose.
DeepLoad takes additional precautions to mask its functionality from security tools. Its operation conceals itself within an executable named “LockAppHost.exe,” which is an authentic Windows process responsible for managing the lock screen, thus blending in with normal Windows activity. The malware enhances its stealth capabilities by disabling PowerShell command history. Instead of employing PowerShell’s built-in commands for launching processes and altering memory, it invokes native Windows core functions directly, thereby bypassing monitoring mechanisms typically associated with PowerShell operations.
To further sidestep detection, DeepLoad generates a secondary component dynamically using the built-in PowerShell feature Add-Type. This feature allows it to compile and run code written in C#, resulting in a temporary Dynamic Link Library (DLL) file that is deposited in the user’s Temp directory. This tactic ensures that the malware avoids detection by using randomized file names for each execution, rendering file-based detection measures ineffective.
Another advanced defense evasion method utilized by DeepLoad is the implementation of asynchronous procedure call (APC) injection. Through this technique, it executes its main payload within a trusted Windows process, thereby avoiding leaving a decoded payload on disk. This involves launching the target process in a suspended state, writing shellcode into its memory, and then resuming the process’s execution. Such clever maneuvers allow the malware to operate invisibly, minimizing the risk of detection.
Moreover, DeepLoad is notable for its credential theft capabilities, systematically extracting browser passwords from infected hosts. It also introduces a malicious browser extension that intercepts user credentials during login processes and persists across user sessions unless deliberately removed. This adds another layer of danger, enabling long-term data theft without user awareness.
A particularly menacing aspect of DeepLoad is its ability to recognize when removable media devices, such as USB drives, are connected. It discreetly copies infected files under seemingly innocuous names like "ChromeSetup.lnk," "Firefox Installer.lnk," and "AnyDesk.lnk." This tactic aims to trigger infections when unsuspecting users double-click on these files, facilitating the malware’s spread.
In a further demonstration of its resilience, DeepLoad has been observed to reinfect a ‘clean’ host utilizing Windows Management Instrumentation (WMI) just three days later without any user action or attacker interaction. This method disrupts conventional detection mechanisms, which often rely on monitoring parent-child process relationships, while also establishing a WMI event subscription that quietly re-executes the attack later on.
The overarching objective of DeepLoad seems to be to create a multi-faceted malware capable of executing a variety of malicious actions throughout the cyber kill chain. It adeptly navigates security controls, intentionally avoids leaving physical artifacts on disk, and integrates seamlessly with Windows processes. This strategy allows it to propagate swiftly across networks, increasing the malware’s potential impact.
The announcement of DeepLoad coincides with reports from G DATA, which recently detailed another malware loader called Kiss Loader. This loader is disseminated through Windows Internet Shortcut files attached to phishing emails, leading users to connect to a remote WebDAV resource. Once activated, it initiates a series of processes that include running malicious scripts and establishing persistence, ultimately downloading the Python-based Kiss Loader.
At this point, the extent of Kiss Loader’s distribution remains uncertain, and it is unclear whether it operates under a malware-as-a-service (MaaS) model. However, the suspected threat actor behind Kiss Loader claims to be from Malawi, adding an additional layer of intrigue to the ongoing investigation into these prolific malware campaigns.
As cyber threats continue to evolve, both researchers and users must remain vigilant against increasingly sophisticated tactics employed by cybercriminals like those behind DeepLoad and Kiss Loader.