In a surprising turn of events, hackers linked to the Chinese government have reportedly maintained access to critical infrastructure in the US for an extended period, according to reports issued by various agencies in February. This revelation marks a shift in Chinese cyber tactics, moving beyond mere espionage to potentially compromising or even destroying infrastructure through operational technology (OT). This includes systems and devices that are programmable and connected to physical environments.
One notable incident occurred last December when a supply chain-focused cyberattack targeted ShipManager software from maritime advisory company DNV, causing disruptions for numerous clients and impacting up to 1,000 vessels. Additionally, the Cybersecurity and Infrastructure Security Agency (CISA) issued warnings about Iranian actors exploiting Unitronics equipment in water and wastewater systems, leading to subsequent alerts from the Environmental Protection Agency (EPA) and the White House. The EPA further cautioned in May that a significant 70% of US water systems do not meet cybersecurity standards.
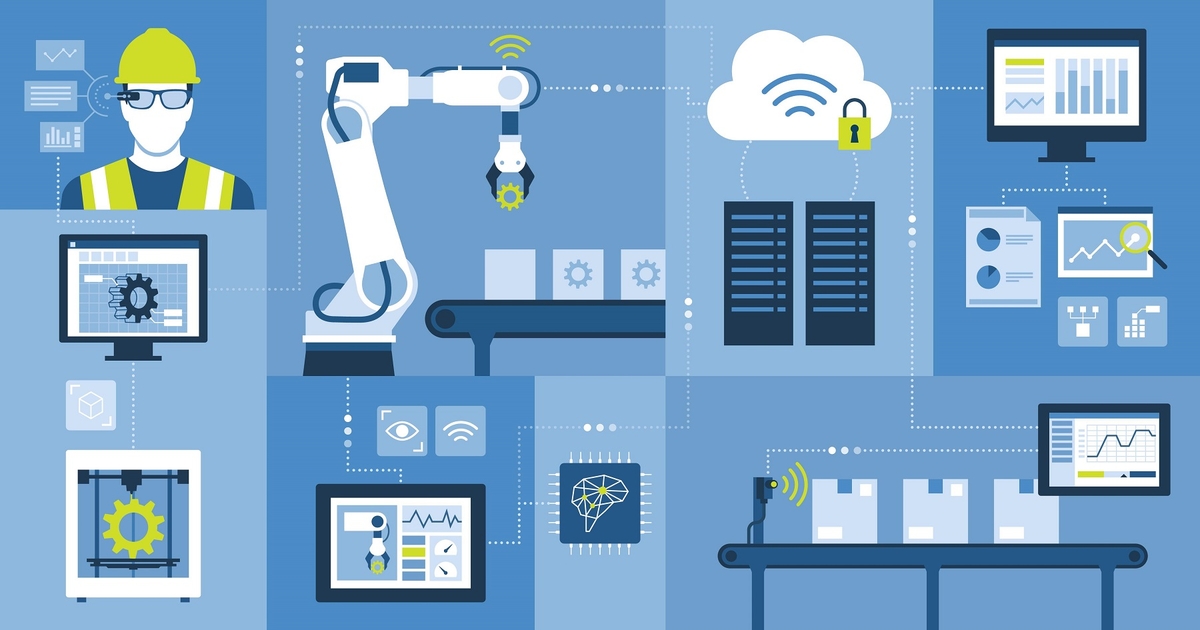
The integration of OT systems with the Internet for remote monitoring and control purposes has inadvertently created vulnerabilities that can be exploited by malicious actors. These systems were initially designed for reliability rather than connectivity, making them challenging to secure and audit effectively.
Attacks on OT, along with infrastructure supporting operational environments, can result in severe consequences such as disruptions to supply chains, equipment damage, and costly production downtime. According to a study by ITC, downtime can cost enterprises anywhere from $1 million to over $5 million per hour. Safeguarding these complex environments requires heightened levels of protection, as a breach in one OT system can have cascading effects on others.
To defend against cyber threats in OT environments, organizations must take proactive steps to mitigate risks and enhance security measures. Implementing the following key strategies can bolster defenses and protect critical infrastructure from malicious actors:
1. Eliminate Gaps Across Environments:
– IT and OT security convergence is crucial for effective risk management.
– Establish cross-functional teams and conduct joint risk assessments.
– Maintain full asset visibility and collaborate with IT teams for continuous monitoring.
2. Develop Comprehensive OT Playbooks:
– Standardize security practices and incident response protocols.
– Consider various scenarios and document response procedures for worst-case scenarios.
– Stay abreast of guidance from relevant organizations and industry groups.
3. Implement Robust Controls:
– Leverage exposure management technology to secure OT systems.
– Combat sophisticated threats like living-off-the-land techniques employed by threat actors.
– Contextualize data and address vulnerabilities proactively to prevent exploitation.
By moving away from reactive policies and adopting a proactive approach to cybersecurity, organizations can effectively reduce risks and safeguard critical infrastructure from cyber threats. While protecting OT environments requires time and effort, enhancing security measures is crucial in defending against prominent APTs and ensuring the integrity of physical environments.