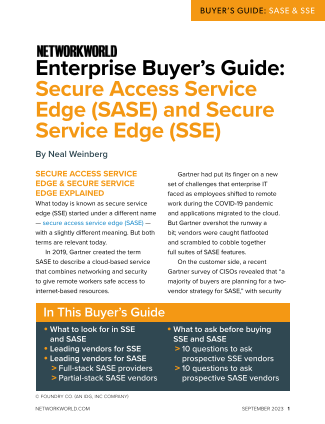
The emergence of Secure Access Service Edge (SASE) and Secure Service Edge (SSE) technologies has been a game-changer for enterprise IT in light of the shift to remote work and cloud-based applications. These advancements have provided solutions to the challenges faced by organizations in ensuring secure access to their networks and data in a distributed work environment.
With the rapid transition to remote work brought on by the COVID-19 pandemic, traditional network security measures have become outdated and incapable of meeting the demands of a dispersed workforce. Employees working from home or off-site locations require seamless and secure access to corporate resources, regardless of their location. This is where SASE and SSE come into play, offering a more holistic and flexible approach to network security that aligns with the needs of modern enterprises.
SASE, in particular, combines network security functions such as SD-WAN, secure web gateways, and Zero Trust security models into a single cloud-based service. This consolidated approach streamlines network management and strengthens security by providing a unified platform for policy enforcement and threat detection. As a result, organizations can ensure consistent protection for their data and applications across various endpoints and network environments.
On the other hand, SSE focuses on enhancing the user experience by optimizing network performance and reducing latency. By leveraging edge computing capabilities, SSE delivers secure and reliable access to cloud-based applications through distributed points of presence. This not only improves application performance but also minimizes the risks associated with data transmission over long distances.
Both SASE and SSE represent significant advancements in network security architecture, offering organizations the ability to adapt to evolving threats and business requirements. By shifting the focus from traditional perimeter-based security to a more dynamic and user-centric approach, these technologies enable organizations to secure their networks without compromising productivity or user experience.
For enterprise IT buyers, understanding the benefits and capabilities of SASE and SSE is crucial in making informed decisions about their network security infrastructure. By evaluating factors such as scalability, ease of deployment, and integration with existing systems, buyers can choose the solution that best suits their organization’s needs and objectives.
In conclusion, the adoption of SASE and SSE technologies has become increasingly vital for organizations looking to secure their networks in the era of remote work and cloud computing. By embracing these innovative approaches to network security, enterprises can enhance their resilience to cyber threats and ensure seamless connectivity for their employees, regardless of their location.