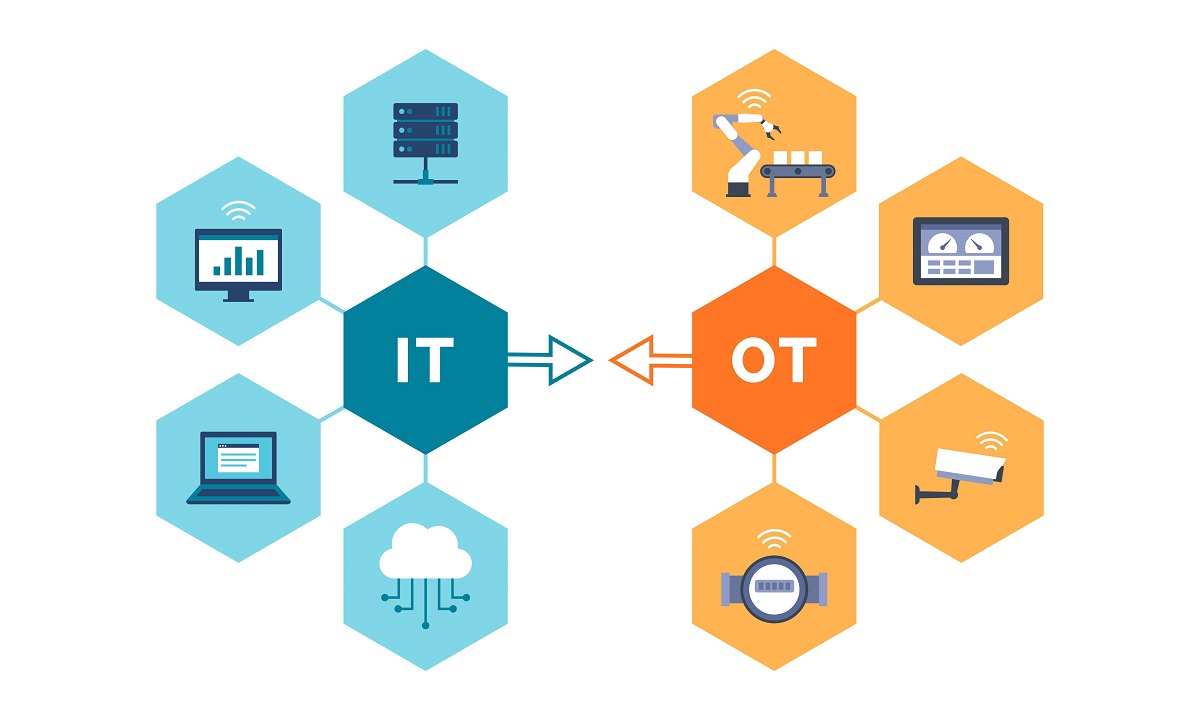
A book set to be launched on November 1, 2023, highlights the fundamental differences between conventional IT networks and operational technology (OT) or industrial control system (ICS) networks and the consequences cyberattacks can have on each. While there are several surface-level differences, such as patching difficulties and the use of outdated protocols in OT networks, the true disparity lies in the consequences of these cyberattacks.
In IT networks, when ransomware attacks occur, the usual response is to detect, respond, and recover. Affected computers are identified and isolated, forensic images are taken, and equipment is erased. The process continues by restoring from backups. In the worst-case scenario, there may be leaks of personally identifiable information (PII) or other sensitive data, leading to potential lawsuits. The primary goal in managing cyber-risk in IT networks is to prevent business consequences by safeguarding the confidentiality, integrity, and availability of business information.
In contrast, the consequences of compromise in OT networks are predominantly physical. Cyberattacks on these networks can lead to catastrophic events such as explosions, industrial malfunctions causing environmental disasters, power outages, or contamination of drinking water. The aim of managing cyber-risk in OT networks is to ensure the correct, continuous, and efficient operation of the physical processes. The focus is not on protecting information but rather on protecting physical operations from cyber-sabotage attacks embedded in information. This fundamental difference between IT and OT networks becomes evident when considering that human lives, damaged turbines, and environmental disasters cannot be “restored from backups.”
Even if industrial networks were fully patched, protected by antivirus software, encrypted, and updated with modern IT cybersecurity mechanisms, this essential distinction would remain. The difference in consequences demands a distinct approach to risk management in safety-critical and reliability-critical networks compared to business networks.
Fortunately, the engineering profession possesses powerful tools to address OT cyber-risks. For instance, mechanical over-pressure valves prevent pressure vessels from exploding and do not contain CPUs, making them unhackable. Similarly, torque-limiting clutches prevent turbines from disintegrating and unidirectional gateways can block attack information from passing. These tools are often overlooked due to their lack of counterparts in the IT security space.
The engineering profession has a long history of managing risks to public safety, leading to its legislated, self-regulating status in many jurisdictions, akin to the medical and legal professions. However, the responsibility and contributions that engineers can make in managing OT cyber-risks are not widely understood. With only a fraction of the number of OT security practitioners compared to IT security practitioners, IT experts are often the initial consultants for industrial cybersecurity solutions. However, most IT security experts are not engineers and may not fully comprehend the role and potential impact of the engineering profession.
There has been progress in developing robust cybersecurity engineering approaches in recent years. For example, the Security PHA Review for Consequence-Based Cybersecurity textbook outlines an approach that incorporates unhackable physical mitigations for cyber threats into routine process hazard analysis (PHA) engineering reviews. Another book by Andrew Bochman and Sarah Freeman, “The Countering Cyber Sabotage: Introducing Consequence-Driven, Cyber-Informed Engineering,” focuses on risk assessment and includes chapters on unhackable mitigations for cyber threats in automation engineering.
In terms of network engineering, the book “Secure Operations Technology” presents different strategies for designing industrial networks that enable information monitoring without introducing vulnerabilities to attacks. Additionally, the US Department of Energy (DOE) released the National Cyber-Informed Engineering Strategy in June 2022, aiming to develop an engineering body of knowledge that can mitigate cyber-enabled attacks or reduce their consequences through design decisions and engineering controls.
The central question addressed by the upcoming book is how much cybersecurity is enough. The level of protection required depends on the consequences that a system or network faces. Safety-critical and critical infrastructure systems demand thorough security measures. However, even the most robust cybersecurity programs cannot provide the level of deterministic protection expected from engineering designs when public safety is at risk.
Implementing security engineering routinely and systematically has the potential to eliminate many safety, reliability, and national security consequences. This could significantly simplify the challenge of determining how much cybersecurity is enough by reducing the strength and cost of programs targeting remaining risks in OT networks. As the crisis of OT shutdowns, equipment damage, and other disastrous consequences caused by cyber attacks looms, the timing is ideal for embracing this new approach to cybersecurity.
More information about the book can be found at the provided link.