The aftermath of the July 19 CrowdStrike glitch continues to create ripples throughout the cybersecurity industry, prompting IT teams to grapple with the arduous task of recovering from the incident. The repercussions of this event are expected to echo for years to come, as organizations navigate through regulatory oversight and confront the stark reality that even a minor error in a software update can have far-reaching global implications.
In the wake of the glitch, cyber adversaries have seized the opportunity to exploit vulnerabilities exposed by the disruption. The faulty sensory configuration update deployed to the Falcon Platform on July 19 triggered widespread Microsoft outages across CrowdStrike’s extensive customer base, which includes major corporations such as Target, Amazon, Alphabet, and Intel. The resulting chaos left employees at these organizations facing system crashes and disruptions, ushering in a period of uncertainty and panic across various sectors, from airports to hospitals to government agencies.
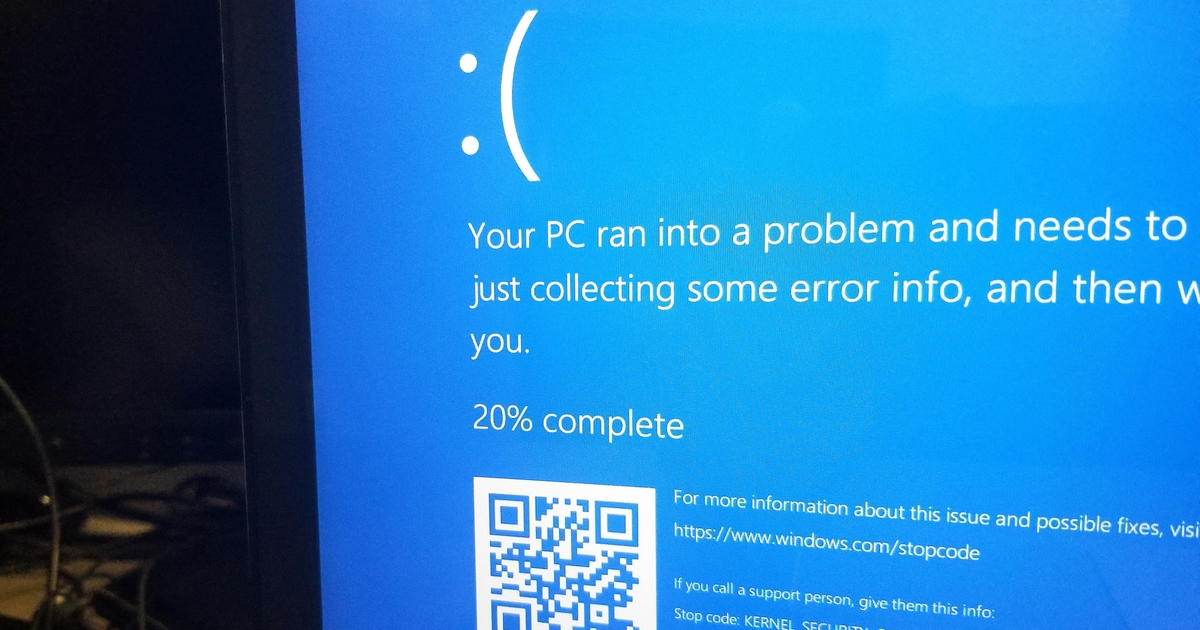
CrowdStrike moved swiftly to clarify that the incident was not a cyberattack but a technical glitch. However, for IT teams tasked with resolving the aftermath, the distinction offered little solace. The recovery process involved manually booting affected PCs into recovery mode, removing the problematic file, and restarting the system – a labor-intensive and time-consuming endeavor that continues to unfold within many organizations.
Tom Marsland, vice president of technology for Cloud Range, emphasized the hands-on nature of the recovery efforts, highlighting the need for manual intervention by IT support personnel on a case-by-case basis. He predicted that the recovery process could stretch over days or even weeks for larger enterprises, underscoring the extensive impact of the glitch on productivity and operational continuity.
While CrowdStrike worked in tandem with Microsoft to address the issue, the fallout affected approximately 8.5 million Windows devices, representing less than 1% of all Windows machines. This incident underscored the interconnectedness of the tech ecosystem, shedding light on the critical importance of robust deployment practices and disaster recovery mechanisms across various stakeholders, as articulated by David Weston, vice president of enterprise and OS security at Microsoft.
The failure of the CrowdStrike update to roll out smoothly raised questions about the company’s testing and deployment procedures. Experts pointed out deficiencies in stress-testing protocols and incremental rollout strategies as key contributing factors to the widespread disruption. The decision to implement the update on a Friday further compounded the challenges faced by IT teams, limiting the availability of resources and increasing the likelihood of issues persisting over the weekend.
As CrowdStrike grapples with the fallout from the glitch, the company is poised to weather a storm of scrutiny and regulatory inquiries, underscoring broader concerns around the consolidation of software vendors and the vulnerabilities inherent in monoculture dependencies within critical industries. The incident also served as a stark reminder of the potential risks posed by a lack of diversity and redundancy in tech infrastructure, prompting calls for a reevaluation of current practices and systems.
In the aftermath of the CrowdStrike outage, adversaries have already begun exploiting the chaos to launch scams and cyberattacks, prompting warnings from industry leaders and cybersecurity experts. CrowdStrike’s CEO and the Cybersecurity and Infrastructure Security Agency (CISA) advised vigilance and caution in dealing with potential threats, urging stakeholders to remain alert and engage only with authorized representatives.
Moving forward, CrowdStrike faces the challenge of rebuilding trust with customers and demonstrating that this incident was an isolated occurrence. While contractual protections may shield the company from legal liabilities, the need to engage in transparent and proactive communication with regulators and clients remains paramount. Ultimately, the fallout from the glitch serves as a stern reminder of the immense responsibility borne by tech companies in safeguarding the integrity and security of global digital infrastructure.