Recent reports from Google’s Threat Intelligence Group have shed light on the increasing threats posed by Russian state-backed actors targeting secure messaging applications like Signal. These actors, suspected to be aligned with Russian intelligence services, are focusing on intercepting sensitive communications of individuals such as military personnel, politicians, journalists, and activists.
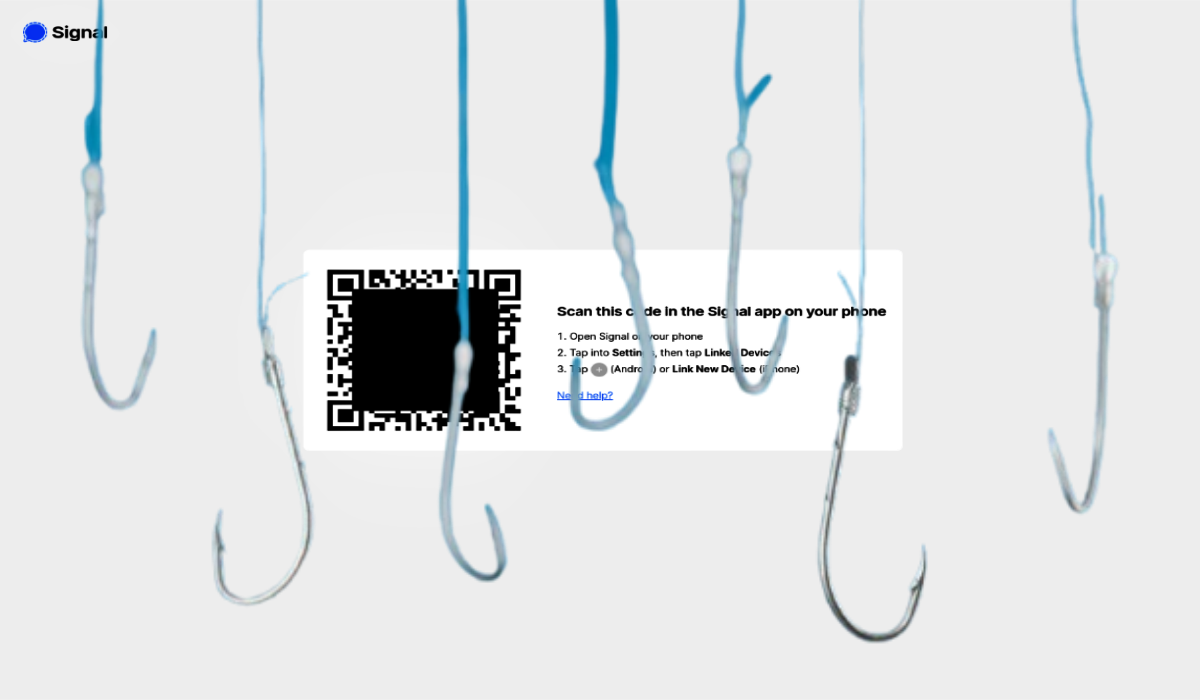
The initial target of these attacks seems to be individuals involved in the conflict in Ukraine. However, experts believe that these tactics will soon extend to other regions and threat actors, posing a significant risk to users of secure messaging apps. One of the primary methods used by these malicious actors involves exploiting the “linked devices” feature of Signal through phishing techniques. By tricking users into scanning malicious QR codes, the attackers can link the victim’s account to a device under their control, allowing them to intercept messages in real-time without compromising the entire device.
These malicious QR codes are often disguised as legitimate Signal resources, such as group invites or security alerts, making it challenging for users to identify the threat. In some cases, these codes are embedded in phishing pages that mimic specialized applications used by organizations like the Ukrainian military. This method of attack can go undetected for extended periods, especially in scenarios where devices are captured on the battlefield by hostile forces.
UNC5792 and UNC4221 are among the identified groups carrying out these attacks. UNC5792 has been observed modifying legitimate Signal group invite links to redirect victims to fake pages, while UNC4221 targets Ukrainian military personnel with malicious QR codes embedded in phishing sites. Apart from phishing, APT44 (Sandworm) utilizes malware and scripts to extract Signal messages from compromised devices, while other groups like Turla and UNC1151 target the desktop application to exfiltrate stored messages.
The popularity of secure messaging apps like Signal has made them prime targets for adversaries, with other platforms like WhatsApp and Telegram also facing similar threats. Researchers have warned about the growing threat to secure messaging applications, highlighting the operational emphasis on Signal from multiple threat actors as a concerning trend that is likely to intensify in the near future.
In light of these risks, users are advised to exercise caution by using strong screen locks with complex passwords, keeping their operating systems and apps updated, and enabling features like Google Play Protect. Regularly auditing linked devices, being cautious with QR codes and links, and enabling two-factor authentication are also recommended practices to enhance security. iPhone users, especially those at high risk, are encouraged to consider enabling Lockdown Mode for added protection against potential attacks.
As the threat landscape continues to evolve, it is essential for users to stay vigilant and take proactive measures to defend themselves against malicious actors seeking to compromise their secure messaging accounts. By staying informed and implementing best practices for cybersecurity, individuals can better protect their sensitive communications from unauthorized interception and exploitation.