Major Security Vulnerability Disclosed in Microsoft Entra ID’s Agent Identity Platform
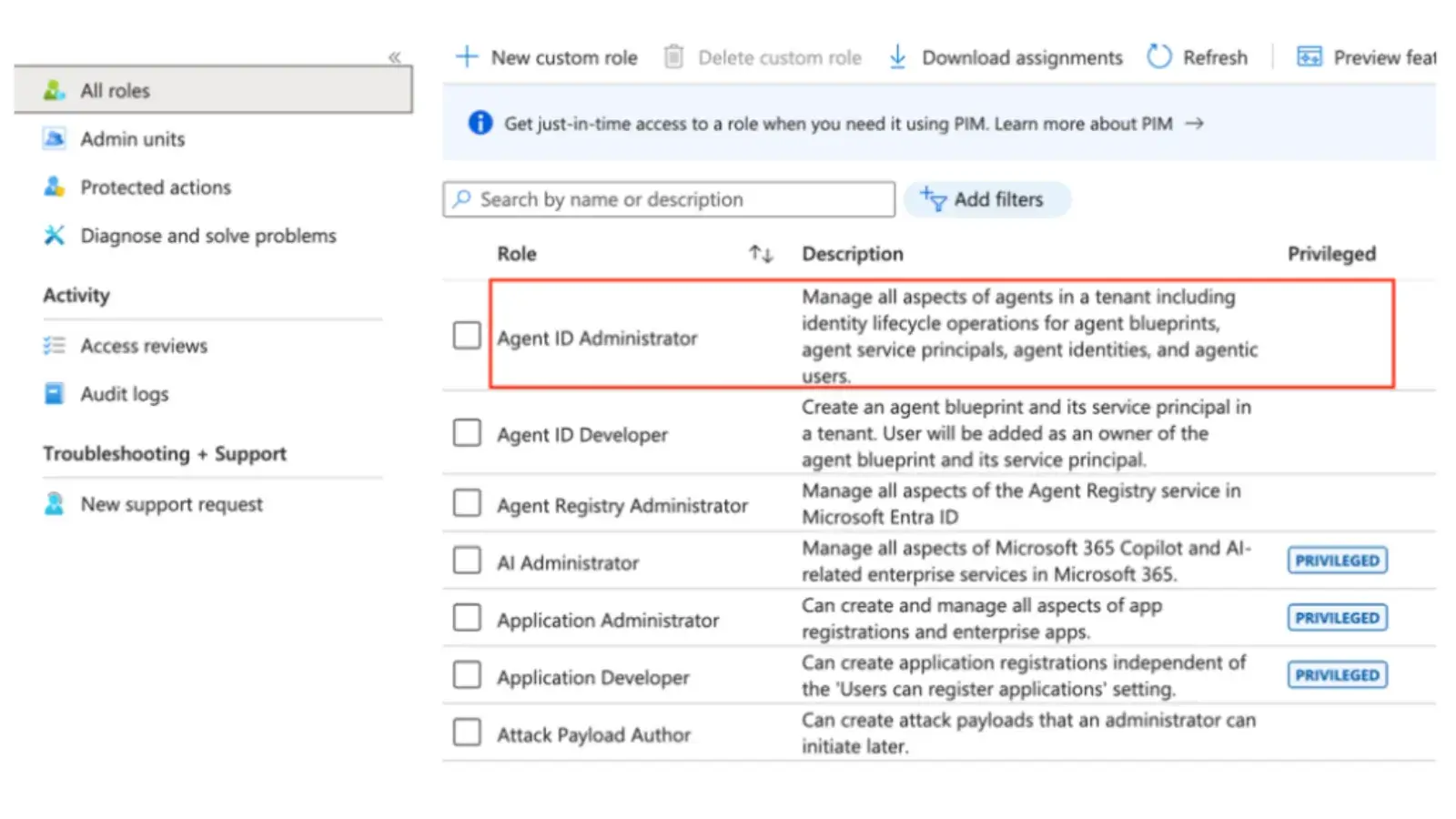
A significant vulnerability has been uncovered within Microsoft’s Entra ID, particularly affecting the newly introduced Agent Identity Platform. Identified as a severe scoping flaw, this security issue allowed individuals assigned the Agent ID Administrator role to seize control of arbitrary service principals across any organization’s tenant, raising substantial concerns regarding potential privilege escalation.
Nature of the Vulnerability
Designed to strictly manage AI agent identities, the Agent ID Administrator role was intended to limit access and control to only those identities. However, a breakdown in structural boundaries inadvertently allowed this administrative role to manipulate non-agent service principals as well. This raised alarms within the cybersecurity community, given that unauthorized access to service principals could lead to substantial privileges being gained without proper oversight.
Microsoft took immediate action to address the vulnerability, implementing comprehensive patches across all cloud environments to safeguard organizations against potential exploitation of this flaw.
Implications for Organizations
The incident underscores the ongoing risks associated with the introduction of new control planes that are built on existing directory primitives. In practice, when an application is registered in Microsoft Entra ID, a global application object and a localized service principal are created. The service principal functions as a localized entity that authenticates and receives role assignments, enabling access to enterprise resources.
The specialized nature of agent identities—designed to govern and secure AI agents as first-class identities—interacts with the foundational infrastructure of conventional enterprise applications. As a result, the roles associated with these new identities necessitate careful scrutiny to ensure robust security.
Exploitation: How Cybercriminals Took Advantage
Cybersecurity researchers from SilverFort disclosed that accounts possessing only the Agent ID Administrator role could exploit this scoping vulnerability to take ownership of any service principal within the organizational domain. This process unfolded through a well-structured yet straightforward attack flow:
-
Assign Unauthorized Ownership: An attacker, holding the Agent ID Administrator role, could assert ownership over any service principal, circumventing the original agent-only restrictions.
-
Generate New Credentials: With ownership established, the attacker was able to create a new secret or certificate, facilitating unauthorized access.
- Authenticate and Hijack: By utilizing the newly generated credentials, the attacker authenticated as the targeted service principal, effectively gaining all associated access rights.
This methodology ultimately provided the attacker with complete control over the compromised application identity. Crucially, attempts to alter ownership on broader application objects were successfully blocked, limiting the vulnerability’s scope.
Risks Posed by the Vulnerability
The most pressing threat stemming from this vulnerability lay in the potential for severe privilege escalation. Service principals often act as the backbone for critical Continuous Integration/Continuous Deployment (CI/CD) pipelines, automated workflows, and high-level security tools. If an attacker managed to hijack a service principal endowed with powerful Microsoft Graph permissions or administrative directory roles, they would instantaneously inherit elevated rights.
Moreover, the relatively new nature of the Agent ID Administrator role raises further concerns, particularly as nearly every enterprise tenant deploys highly privileged service principals for operational needs. The Entra user interface did not visibly flag the Agent ID Administrator role as privileged, potentially misleading IT administrators into assigning this role without sufficient security evaluations.
Remediation and Recommendations
Following responsible disclosure practices in February 2026, Microsoft verified the existence of the flaw and rolled out an extensive fix by April 9, 2026. As a security measure, the Agent ID Administrator role has now been permanently restricted from modifying the ownership of non-agent service principals.
Given the alarming nature of the incident, organizations are urged to actively monitor the usage of sensitive roles and to promptly alert security teams regarding any unexpected changes in service principal ownership. Privileged service principals should be treated as critical infrastructure, necessitating continuous auditing of any credentials that are newly created.
As cybersecurity threats are ever-evolving, organizations are reminded of the importance of vigilance in monitoring their security postures and adapting their defenses accordingly.