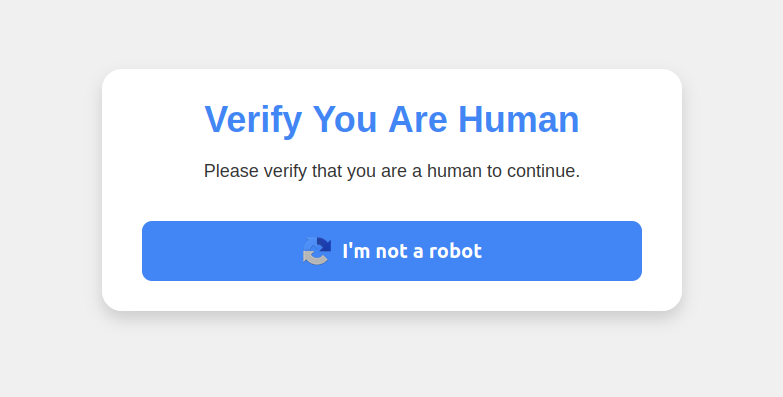
A new malware deployment strategy known as ClickFix has become more widespread, following its initial appearance in targeted attacks last year. This devious scheme involves tricking visitors to a hacked or malicious website into downloading password-stealing malware by pretending to be a CAPTCHA test designed to verify human users. The perpetrator behind this scam has developed a series of keypress actions that, when completed by the user, prompt Windows to download and launch malicious code through the mshta.exe program.
The ClickFix attacks begin with a website popup that asks the user to prove their humanity by completing three sequential steps. The first step requires pressing the Windows key and the letter “R” simultaneously, which opens the Windows “Run” prompt to execute a specified program. The second step instructs the user to press the CTRL key and the letter “V” at the same time, which pastes malicious code from the site’s virtual clipboard. Finally, the third step involves pressing the Enter key, triggering Windows to download and execute the malicious code through mshta.exe, which can lead to the installation of various malware families such as XWorm, Lumma stealer, VenomRAT, AsyncRAT, Danabot, and NetSupport RAT.
In a recent blog post, Microsoft revealed the extent of the ClickFix campaign, highlighting the diverse range of malware payloads delivered through this deceptive tactic. The attackers often impersonate legitimate organizations like Booking.com to lure unsuspecting victims into clicking through these malicious prompts. By sending emails that appear to be from Booking.com and referencing various scenarios like negative reviews or online promotions, cybercriminals aim to exploit individuals, especially those working in industries like hospitality and healthcare.
Notably, the healthcare sector has also been targeted by ClickFix attacks, with cybersecurity firm Arctic Wolf warning about malicious code embedded in the popular physical therapy video site HEP2go. The redirection to a ClickFix prompt through legitimate websites underscores the sophistication and evolving nature of these phishing tactics. The U.S. Department of Health and Human Services issued an alert in October 2024, cautioning about the diverse forms that ClickFix attacks can take, including fake Google Chrome error pages and Facebook popups.
The prevalence of ClickFix attacks highlights the need for enhanced cybersecurity measures, especially in preventing unsuspecting users from falling victim to social engineering techniques. Organizations can leverage Microsoft Group Policy restrictions to disable the “run” command triggered by specific key combinations, fortifying their defenses against malware threats that exploit vulnerable user interactions. As the cybersecurity landscape continues to evolve, maintaining vigilance and implementing robust security protocols are essential in safeguarding against the ever-present threat of sophisticated cyber attacks.