A new report from cybersecurity researchers at Group-IB has revealed that a large Chinese-language hacking group has developed a sophisticated banking Trojan known as “GoldPickaxe.” This malware is designed to deceive individuals into providing sensitive information such as personal IDs, phone numbers, and face scans, which the hackers then use to gain unauthorized access to the victims’ bank accounts.
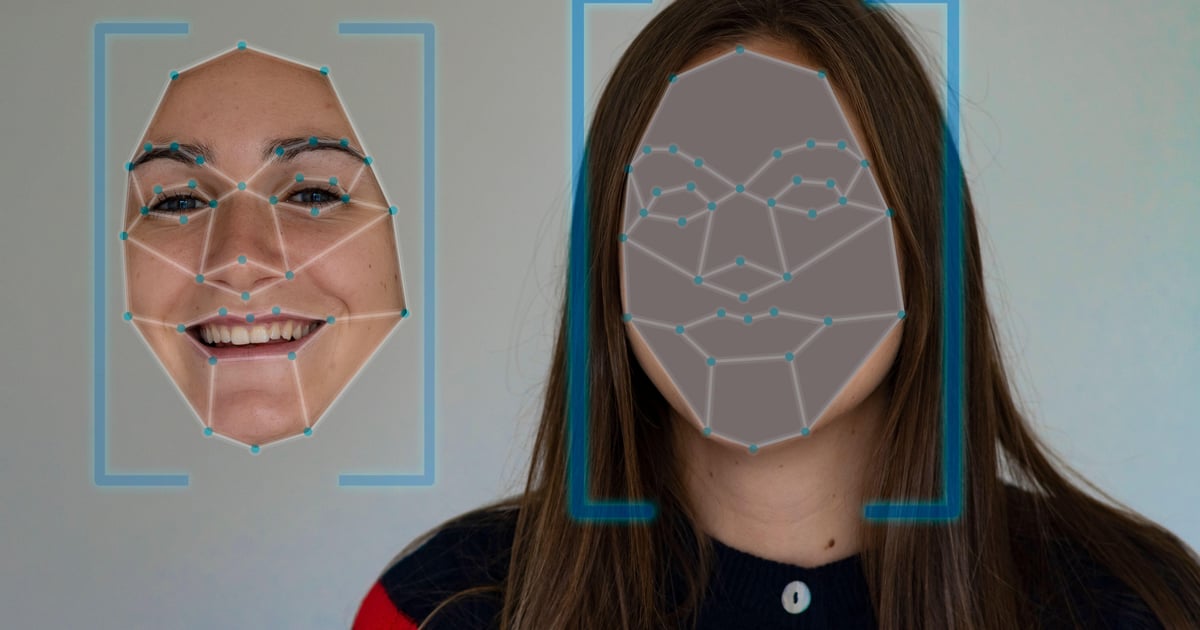
According to the report, the GoldPickaxe Trojan is capable of operating across both iOS and Android devices. The attackers have been observed using the malware to pose as a government service app, particularly targeting elderly victims who are then prompted to scan their faces. The compromised face scans are then used to create deepfake images, allowing the hackers to bypass advanced biometric security measures employed by several Southeast Asian banks.
The research conducted by Group-IB identified an early victim of the GoldPickaxe Trojan, a Vietnamese citizen who reportedly lost approximately $40,000 due to the fraudulent scheme.
The effectiveness of the GoldPickaxe Trojan is attributed to several factors. One significant reason is that advancements in deepfake technology have now allowed it to keep pace with biometric authentication mechanisms. Additionally, many individuals have not yet realized the extent to which deepfake technology can be exploited by threat actors to carry out malicious activities.
Andrew Newell, the Chief Scientific Officer at iProov, emphasized the power and control that face swap technology affords to hackers. He highlighted the need for increased vigilance in recognizing the potential threats posed by these advancements.
Following this development, there is growing concern over the ability of financial institutions to safeguard their customers’ data and prevent unauthorized access to their accounts. Last March, the Bank of Thailand announced new policy changes aimed at combating financial fraud, including requiring facial recognition for significant customer transactions. However, just three months after the enforcement of these measures, the GoldPickaxe Trojan emerged in the wild, evading the bank’s security protocols.
The Trojan, which was built upon an existing malware called “GoldDigger,” was initially identified by the Banking Sector CERT in Thailand. It was found to be disguised as a legitimate app known as “Digital Pension,” used by elderly individuals to receive pensions in digital format.
Unlike some other banking trojans that operate as an overlay on top of legitimate banking apps, GoldPickaxe collects the necessary information to allow attackers to manually access their victims’ bank accounts and bypass authentication checks.
Andrew Newell emphasized the need for banking institutions to adapt to the evolving threat landscape, acknowledging that the rate of evolution of cyber threats has significantly accelerated. There is a call for banks to adopt a different approach to effectively address these emerging challenges.
Group-IB recommends that banks implement robust user session monitoring and advises customers to exercise caution when clicking on links, only download applications from official app stores, review app permissions, avoid adding unknown contacts, verify the legitimacy of communications from their bank, and promptly report any suspected fraudulent activity to their bank.
The emergence of the GoldPickaxe Trojan and its potential impact on the security of financial institutions underscores the ongoing need for proactive and adaptive measures to mitigate the risks posed by cyber threats. As technology continues to evolve, it is essential for organizations and individuals to remain vigilant and continually update their security practices to safeguard against malicious activities.