North Korea-linked threat groups have been utilizing living-off-the-land (LotL) techniques and trusted services to fly under the radar, with a recent campaign by Kimsuky shedding light on their use of PowerShell scripts and storing data in Dropbox folders, coupled with enhanced operational security measures.
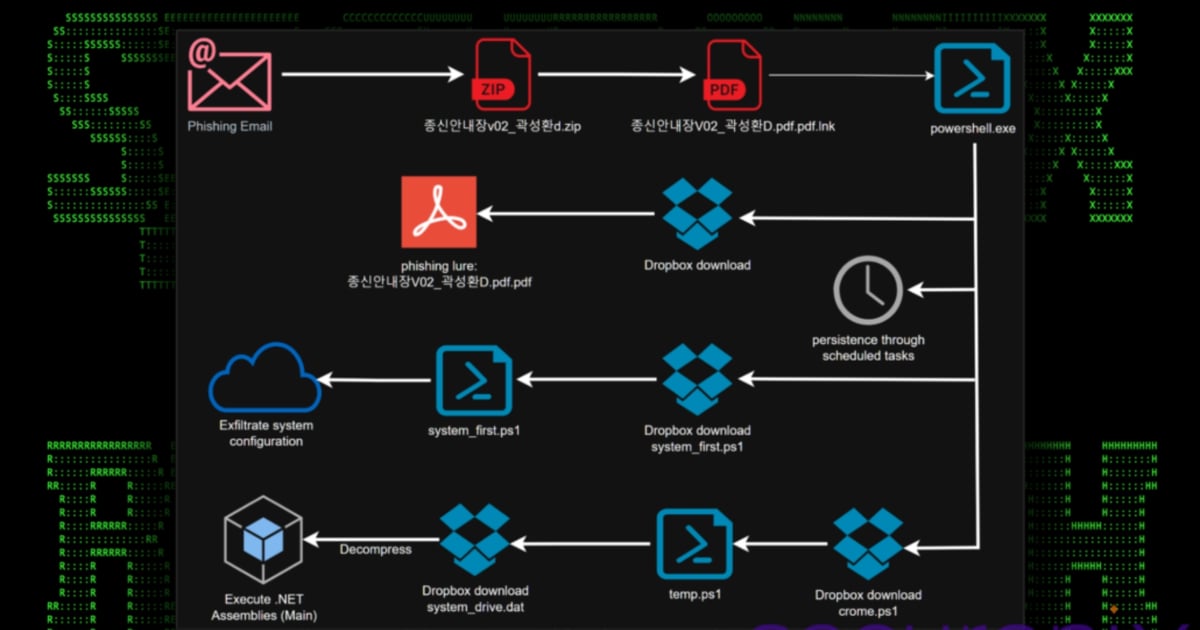
Dubbed “DEEP#DRIVE” by cybersecurity firm Securonix, the campaign employed fake work logs, insurance documents, and crypto-related files to lure users into downloading and running a zipped shortcut file that collects system configuration information and then executes PowerShell and .NET scripts. The attack tools then upload the system data to Dropbox folders and fetch additional commands and capabilities for further compromise.
Although there was some indication of a focus on quick financial gains, like targeting cryptocurrency users, the primary objective of the threat group seemed to be the theft of sensitive data from South Korean government agencies and businesses, as per Tim Peck, a senior threat researcher at Securonix.
Throughout the years, North Korean cyber-operations groups have frequently targeted South Korea and the US, with South Korean government agencies and companies being among the prime targets. In September 2024, the FBI cautioned about North Korean groups planning to launch a surge of attacks against organizations with substantial cryptocurrency reserves, and Kimsuky executed a similar multistage attack against South Korean targets the previous year.
Kimsuky is not a singular entity but comprises five threat groups with some overlapping characteristics, according to threat intelligence firm Recorded Future. While one group focuses on the healthcare and hospitality sectors, another zeroes in on cryptocurrency markets, showcasing the diverse interests within the organization.
The Kimsuky groups emerged as the most active North Korean threat actors between 2021 and 2023, outmatching other well-known North Korean groups like Lazarus and Andariel in terms of attack volume. These groups predominantly conduct high volume phishing campaigns, especially targeting entities in South Korea, rather than personalized spear-phishing endeavors, as noted by Mitch Haszard, senior threat intelligence analyst at Recorded Future.
In the wake of the DEEP#DRIVE campaign, it was discovered that the Kimsuky group had managed to pilfer data from over 8,000 system configuration files, showcasing a substantial impact on victim organizations. The compromised data included host IP addresses, system uptime, OS details, security software info, and running processes, providing the attackers with valuable insights.
Moreover, the campaign highlighted Kimsuky’s advancements in operational security, employing OAuth-based authentication on Dropbox folders to evade traditional defenses and promptly dismantling components of their infrastructure to thwart investigation efforts. This level of operational awareness is not typically seen in phishing-driven malware campaigns, signifying a concerning trend in cyber-operations tactics.
For companies facing such threats, disabling hidden file extensions, blocking shortcut files from executing in user folders, and permitting only signed PowerShell scripts to run are crucial countermeasures to detect and prevent similar attacks. Additionally, organizations in targeted industries must enhance email security and conduct regular training sessions for employees to recognize and mitigate phishing threats, emphasizes Haszard from Recorded Future.
As the cybersecurity landscape continues to evolve, staying vigilant against sophisticated threat groups like Kimsuky is imperative to safeguard sensitive data and maintain operational resilience in the face of persistent cyber threats.