MasterCard, the popular payment card giant, recently addressed a major error in its domain name server settings that left the company vulnerable to potential interception or redirection of Internet traffic had a cybercriminal registered an unused domain name. The misconfiguration went unnoticed for almost five years until a security researcher, Philippe Caturegli, took action by spending $300 to register the domain and prevent it from falling into the wrong hands.
Between June 30, 2020, and January 14, 2025, one of MasterCard’s core Internet servers, used to direct traffic for parts of the mastercard.com network, was found to have a misconfigured domain. The company relies on five shared DNS servers provided by internet infrastructure provider Akamai to translate website names into numeric Internet addresses for efficient computer management. However, one of these Akamai DNS servers was mistakenly configured to use the domain “akam.ne” instead of the correct ending “akam.net.”
Caturegli, the founder of security consultancy Seralys, discovered this critical error and took the initiative to secure the domain under the jurisdiction of Niger’s top-level domain authority. Upon enabling a DNS server on akam.ne, he observed a significant influx of DNS requests hitting his server daily from various locations worldwide. Although MasterCard was the largest entity affected by this misconfiguration, it was evident that other organizations had made similar errors with their DNS entries.
The potential risks associated with this misconfiguration were significant. Caturegli could have intercepted wayward emails directed towards mastercard.com or other affected domains, obtained authorized website encryption certificates for relaying web traffic, or even passively acquired sensitive information like Microsoft Windows authentication credentials. Despite these possibilities, Caturegli refrained from exploiting the situation and promptly notified MasterCard about the issue.
Upon receiving the notification, MasterCard acknowledged the mistake and assured that there was no real threat to its systems’ security. The company claimed to have corrected the typo promptly to mitigate any potential risks posed by the misconfigured DNS server. However, Caturegli received a request through Bugcrowd, a platform that rewards security researchers for identifying flaws and working with affected vendors to resolve them, asking him to remove his public disclosure of the MasterCard DNS error shared on LinkedIn.
Caturegli clarified that he reported the issue directly to MasterCard and took the necessary steps to prevent exploitation before making any public disclosure. He emphasized his commitment to ethical security practices and responsible disclosure by ensuring that the affected domain was secured at his own expense. Despite his efforts, Caturegli expressed disappointment with MasterCard’s response and highlighted the DNS lookups recorded before reporting the issue to showcase the potential risks associated with the misconfigured domain.
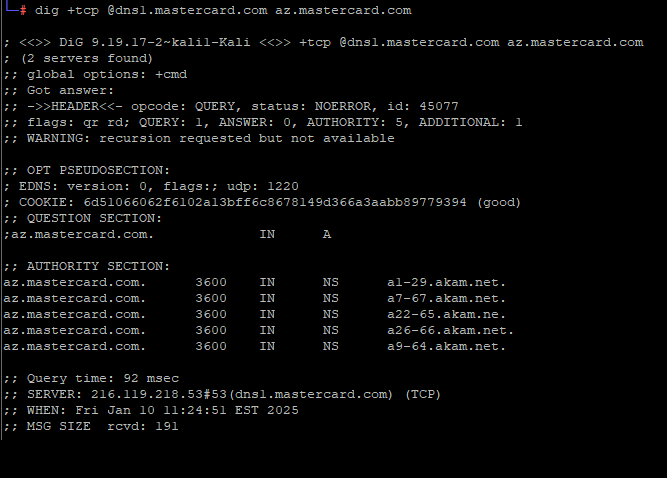
The misconfigured DNS server in question, az.mastercard.com, was identified as a subdomain linked to production servers at Microsoft’s Azure cloud service. While the exact function of this subdomain remains unclear, its association with Azure suggests it plays a crucial role in MasterCard’s network infrastructure. Caturegli concluded his LinkedIn post by cautioning organizations against dismissing risks and advocating for a proactive approach to security disclosures.
Interestingly, the domain akam.ne had been registered previously in 2016 by an individual using a Yandex email address from Moscow, Russia. The domain’s history revealed that it was connected to an internet server in Germany between 2016 and 2018 before expiring. This discovery aligns with a report by an ex-Cloudflare employee on a similar typo domain registered for organizations mistyping their AWS DNS server, highlighting the potential risks associated with minor domain name errors.
In conclusion, the MasterCard DNS error serves as a reminder of the importance of maintaining accurate domain configurations to safeguard against potential security threats. Caturegli’s proactive approach to addressing the issue underscores the significance of responsible vulnerability disclosure in promoting a secure online environment for businesses and consumers alike.