A new cybersecurity report from The Hacker News has revealed a dangerous hacking campaign linked to North Korea that uses everyday communication tools to spread malware. The attack focuses on targeting individuals through phishing emails and then exploiting their trusted messaging networks.
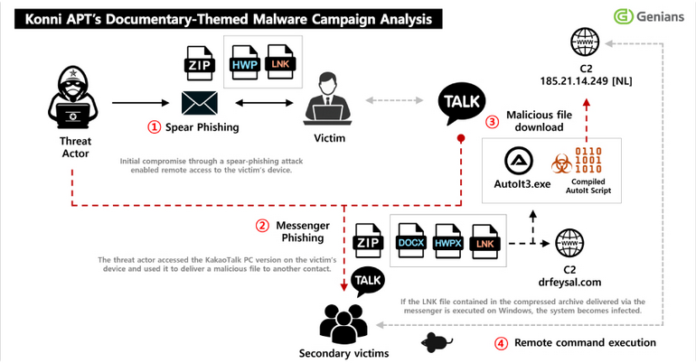
The campaign begins when a victim receives a carefully crafted email designed to look legitimate. Once the attached file is opened, it installs a malicious program known as EndRAT onto the victim’s device. This malware allows attackers to gain full access to the system, including the ability to monitor activity, steal sensitive data, and maintain long-term control without being detected.
What makes this attack especially concerning is its use of KakaoTalk, a widely used messaging platform. After infecting a device, the hackers use the victim’s KakaoTalk account to send malicious messages to their contacts. Because these messages come from a trusted source, recipients are much more likely to open them, allowing the malware to spread quickly and quietly.
Cybersecurity experts believe this operation is part of a broader espionage effort rather than simple cybercrime. Instead of seeking immediate financial gain, the attackers aim to gather intelligence and maintain persistent access to targeted systems. This reflects a growing trend where hacking groups act more like state-sponsored intelligence agencies.
The incident highlights how modern cyberattacks are evolving. Hackers are no longer relying only on technical vulnerabilities but are increasingly exploiting human trust and everyday digital platforms. As messaging apps and email remain essential tools for communication, they are also becoming key targets for cyber threats.
In conclusion, this attack serves as a reminder that cybersecurity is not just about technology but also about awareness. Users should be cautious when opening unexpected emails or files, even if they appear to come from someone they know. As hackers continue to develop more sophisticated methods, staying alert is one of the best defenses against these evolving threats.