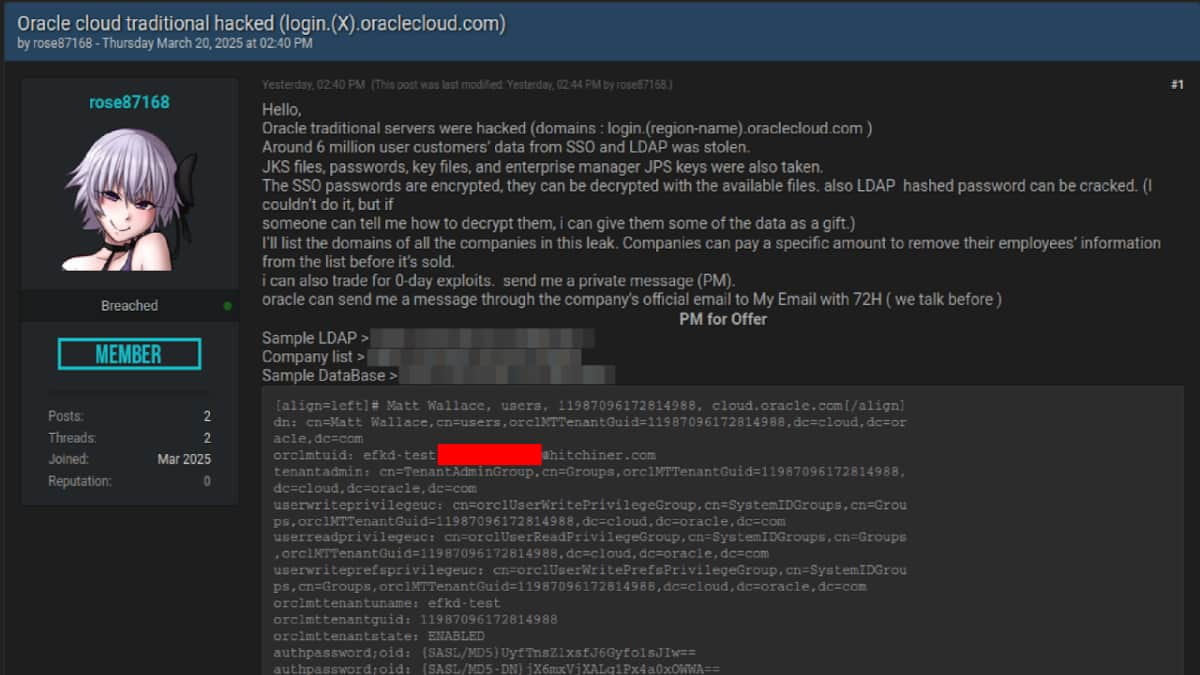
In a recent development, CloudSEK’s XVigil platform has exposed a cyberattack on Oracle Cloud, resulting in the exfiltration of a staggering six million records and potentially impacting over 140,000 tenants. The perpetrator behind this attack, identified as ‘rose87168,’ has stolen sensitive data such as JKS files, encrypted SSO passwords, key files, and enterprise manager JPS keys. These stolen data sets are currently being traded on Breach Forums and other dark web platforms.
The attacker has been active since January 2025 and claims to have compromised a subdomain, login.us2.oraclecloud.com, which has now been shut down. This subdomain was found hosting Oracle Fusion Middleware 11G, as evidenced by a Wayback Machine capture from February 17, 2025. The attacker is demanding ransom payments from affected tenants for the removal of their data and has even offered rewards for assistance in decrypting the stolen SSO and LDAP passwords.
CloudSEK’s analysis suggests that the threat actor may have exploited a vulnerable version of Oracle Cloud servers, possibly leveraging an older flaw known as CVE-2021-35587. This particular vulnerability affects Oracle Fusion Middleware (OpenSSO Agent) versions 11.1.2.3.0, 12.2.1.3.0, and 12.2.1.4.0. Initially added to the CISA KEV catalog in December 2022, this vulnerability enables unauthenticated attackers to compromise Oracle Access Manager, potentially resulting in a complete system takeover. The exploitation of this vulnerability aligns with the stolen data and the attacker’s actions, indicating a significant security lapse on Oracle’s part.
Furthermore, it was discovered that the Oracle Fusion Middleware server had not been updated since September 27, 2014, suggesting the use of outdated software. CloudSEK researchers highlighted the lack of patch management practices and insecure coding as contributing factors to the exploitation of this vulnerability. This flaw allowed the threat actor to gain unauthorized access to Oracle Access Manager and subsequently compromise the Oracle Cloud environment.
Despite CloudSEK’s findings and the attacker’s claims, Oracle has vehemently denied any breach of its cloud infrastructure. The company stated that there was no breach of Oracle Cloud and that the published credentials were not for their platform. However, the potential impact of such a breach cannot be understated, with the exposure of six million records posing a significant risk of unauthorized access and corporate espionage. The theft of JKS files containing cryptographic keys and encrypted SSO and LDAP passwords could lead to further breaches within Oracle Cloud environments.
In response to this incident, CloudSEK recommends immediate credential rotation, thorough incident response and forensics, continuous threat intelligence monitoring, and engagement with Oracle Security for verification and mitigation. Strengthening access controls is also advised to prevent future security incidents and safeguard sensitive data within Oracle Cloud.
As the investigation continues, the security and privacy of Oracle Cloud customers remain a top priority, emphasizing the need for robust cybersecurity measures to protect against evolving cyber threats and data breaches.