A cybersecurity researcher, Oleg Zaytsev, uncovered a widespread campaign known as “360XSS,” exploiting a vulnerability in the Krpano virtual tour framework. This attack involved manipulating search engine results and distributing spam advertisements across over 350 websites, including government portals, universities, and news outlets.
Krpano is a popular software tool that allows users to create immersive 360° experiences, enabling them to explore panoramic images and videos in a virtual environment. Zaytsev’s research revealed that the campaign leveraged a reflected cross-site scripting (XSS) flaw in the Krpano VR library, identified as CVE-2020-24901. The vulnerability existed in a configuration setting within the Krpano framework that allowed query parameters to be passed directly into the framework’s configuration, leading to the injection of arbitrary XML and the reflected XSS.
Despite patches being released to address the vulnerability, many websites, including the developer’s own site, remained unpatched, leading to widespread exploitation. The discovery of the campaign began when adult content search results appeared under a prestigious university’s domain, indicating that a specific parameter within the URL was being exploited to inject malicious code. This code redirected users to spam advertisements, revealing a sophisticated attack strategy beyond simple website defacement.
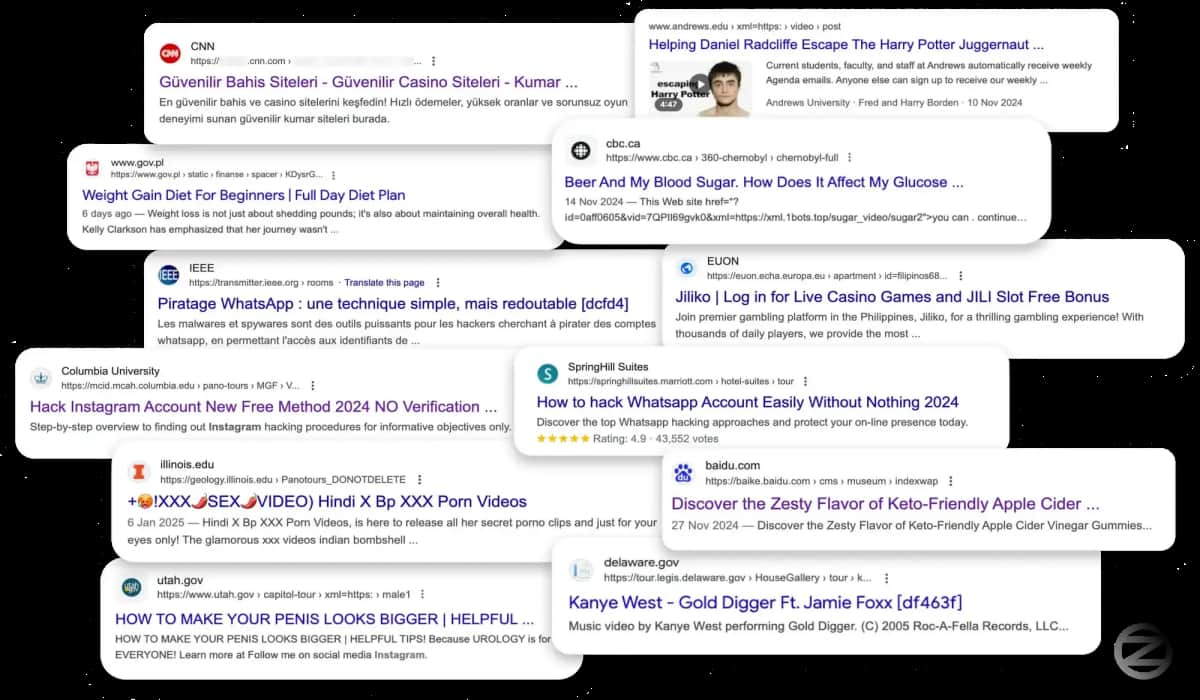
The scale of the campaign was extensive, compromising over 350 websites across various sectors, including government portals, universities, news outlets, and major corporations. Attackers utilized the XSS vulnerability to inject malicious scripts that manipulated search engine results, utilizing SEO poisoning to boost the visibility of spam advertisements.
The impact of the campaign extended to sensitive government portals, major universities, reputable news outlets, and Fortune 500 companies, suggesting a calculated approach by potentially an Arab group. The focus on distributing advertisements rather than direct attacks on user data indicated a strategic intent behind the campaign.
Zaytsev noted in a blog post that the perpetrators behind the campaign remained elusive, but clues pointed towards the involvement of an Arab group based on the ads and patterns observed during the investigation. Efforts to report the vulnerability to affected organizations were challenging, with many lacking formal disclosure programs. However, some organizations responded positively, and the Krpano developers addressed the issue with a patch in a subsequent release, advising organizations to update to the latest version and disable the vulnerable configuration setting.
Eran Elshech, Field CTO at Seraphic Security, emphasized that attackers are increasingly exploiting browser vulnerabilities and web frameworks instead of traditional malware. The 360XSS campaign exemplifies how easily a known XSS flaw can be utilized to compromise trusted sites, manipulate search results, and use web properties for spam ads. He warned that the scalability and stealth of such attacks make them highly effective, enabling attackers to infiltrate high-traffic sites and reach large audiences without direct access to user devices.
In conclusion, the 360XSS campaign underscores the importance of promptly addressing vulnerabilities in web frameworks and the need for organizations to stay vigilant against such sophisticated cyber threats.