Security researcher Thomas Lambertz recently demonstrated new attack tactics during the Chaos Communication Congress in Germany. Lambertz revealed that a previously patched flaw in Windows BitLocker disk encryption is still vulnerable to attacks that could potentially allow hackers to decrypt sensitive information.
The flaw in question, tracked as CVE-2023-21563, was thought to have been addressed by a Microsoft patch. However, Lambertz’s research showed that the flaw can still be exploited over the network, contrary to Microsoft’s analysis. By plugging in a USB device and utilizing PXE booting, Lambertz was able to exploit the vulnerability without physical access to the device.
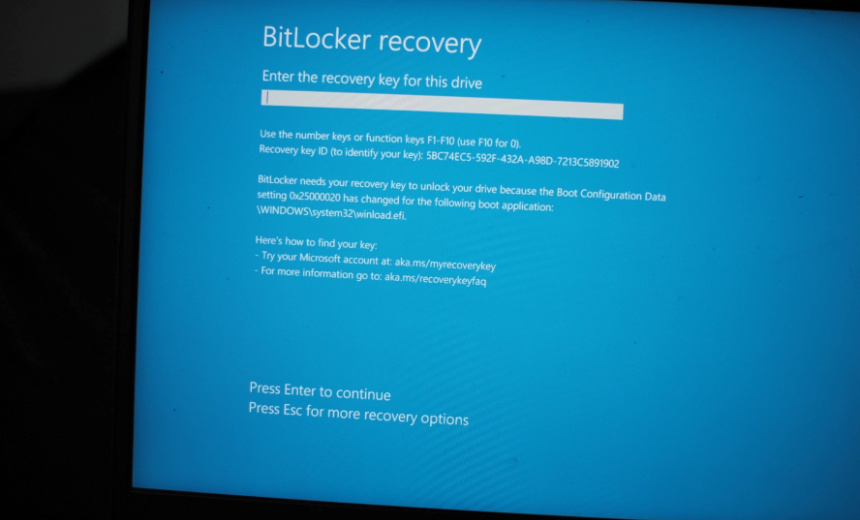
During his presentation, Lambertz showcased a tactic called “bitpixie” that takes advantage of weaknesses in how Windows devices handle memory and encryption processes during booting and recovery. By rebooting the device in recovery mode and running a downgraded version using a Windows bootloader, Lambertz was able to trick the device into forgetting its encryption key. This allowed him to access the system memory and extract the master key needed to decrypt the data.
To mitigate the risk of such attacks, Lambertz suggested disabling the full network stack in the BIOS to prevent PXE booting. However, he noted that Microsoft is facing challenges in balancing security updates with the risk of rendering legacy devices inoperable.
According to Lambertz, Microsoft is hesitant to issue firmware updates that could potentially disrupt the functionality of BitLocker. He highlighted the company’s dilemma in deciding whether to renew its current boot certification, which is set to expire in 2026. Failure to renew the certification could lead to security vulnerabilities, but renewing it may also pose compatibility issues for older devices.
Lambertz expressed concern that allowing the use of old, unsecured certificates could create chaos in the security landscape. He emphasized the need for Microsoft to find a solution that ensures both security and compatibility for devices using BitLocker encryption.
In response to Lambertz’s findings, Microsoft has not yet provided a comment on the issue. As the debate continues on how to address the lingering vulnerability in BitLocker, it remains crucial for organizations and users to stay vigilant about their encryption key management practices to safeguard against potential attacks.