Security experts have recently uncovered a sophisticated memory-only dropper known as PEAKLIGHT, which is linked to a complex multi-stage malware infection process. This new threat is concerning due to its ability to operate stealthily and evade traditional detection methods.
PEAKLIGHT is designed to function without leaving any traces on the disk, making it extremely difficult to detect. It employs various obfuscation techniques to conceal its malicious activities, adding to the challenge of identifying and mitigating the threat.
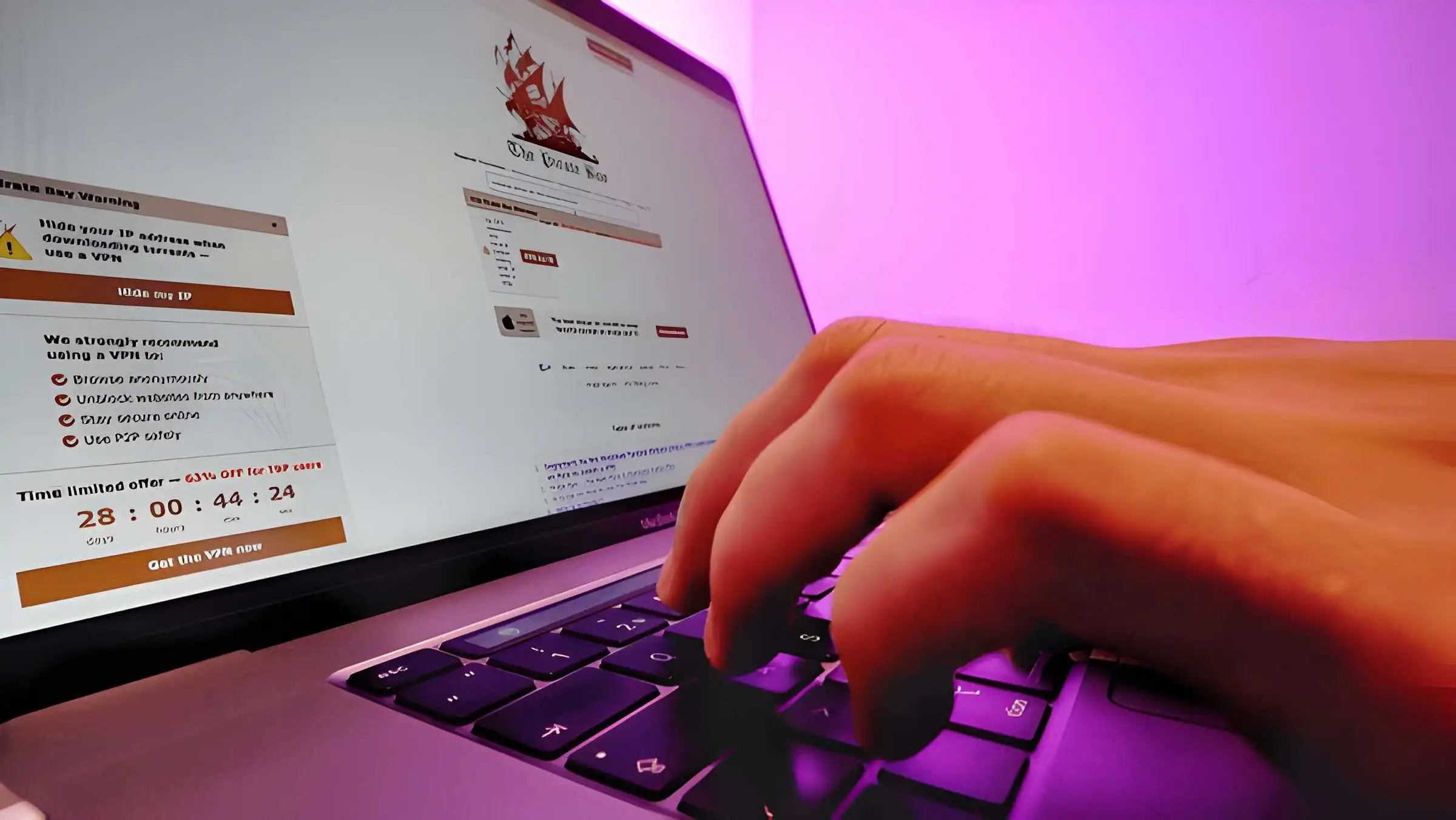
The infection process begins with unsuspecting users downloading pirated movie files that are actually malicious ZIP files in disguise. These files contain Microsoft Shortcut Files (LNK) that serve as a trigger to kick off the infection process.
Upon executing the LNK files, a PowerShell script is invoked, which then downloads additional malicious content from a remote server. The attackers behind PEAKLIGHT have demonstrated their expertise by using two different variations of PowerShell scripts to bypass traditional security measures, highlighting the sophistication of their tactics.
After the initial infection stage, PEAKLIGHT progresses to its second phase, where a JavaScript-based dropper hidden in the victim’s system memory decodes and executes the final downloader. This downloader, also known as PEAKLIGHT, comes in two main variations, each with unique characteristics but sharing the common goal of downloading additional malicious files from a content delivery network (CDN).
One of the key distinguishing features of PEAKLIGHT is its ability to check for specific ZIP archives in hardcoded file paths. If these archives are missing, the malware downloads them from a CDN. PEAKLIGHT has been observed downloading various payloads, including LUMMAC.V2, SHADOWADDER, and CRYPTBOT, each serving a different malicious purpose.
Different variations of PEAKLIGHT exhibit distinct behaviors, such as target directories, execution logic, and downloaded file names. The malware utilizes complex obfuscation techniques like hexadecimal and Base64 encoding to obfuscate the true nature of its payloads, further complicating detection and analysis efforts.
To protect against the PEAKLIGHT threat, researchers recommend scanning environments for potential indicators of compromise (IOCs) and utilizing YARA rules. Keeping security software updated to detect and block malicious activities is also essential, along with exercising caution when dealing with suspicious emails and attachments, particularly those offering pirated content. Practicing safe browsing habits and avoiding clicking on unknown links can also help mitigate the risk of falling victim to PEAKLIGHT’s malicious activities.
The emergence of PEAKLIGHT underscores the effectiveness of memory-only techniques in evading detection and the danger posed by the distribution of malicious payloads through seemingly harmless channels like pirated content and trusted system processes. It serves as a reminder of the need for vigilance and proactive cybersecurity measures in the face of evolving and sophisticated cyber threats.