The total volume of ransom payments has seen a significant decrease of approximately 35% compared to the previous year, attributed to the efforts of law enforcement and an increasing number of victims choosing not to pay, as reported by blockchain analytics company Chainalysis.
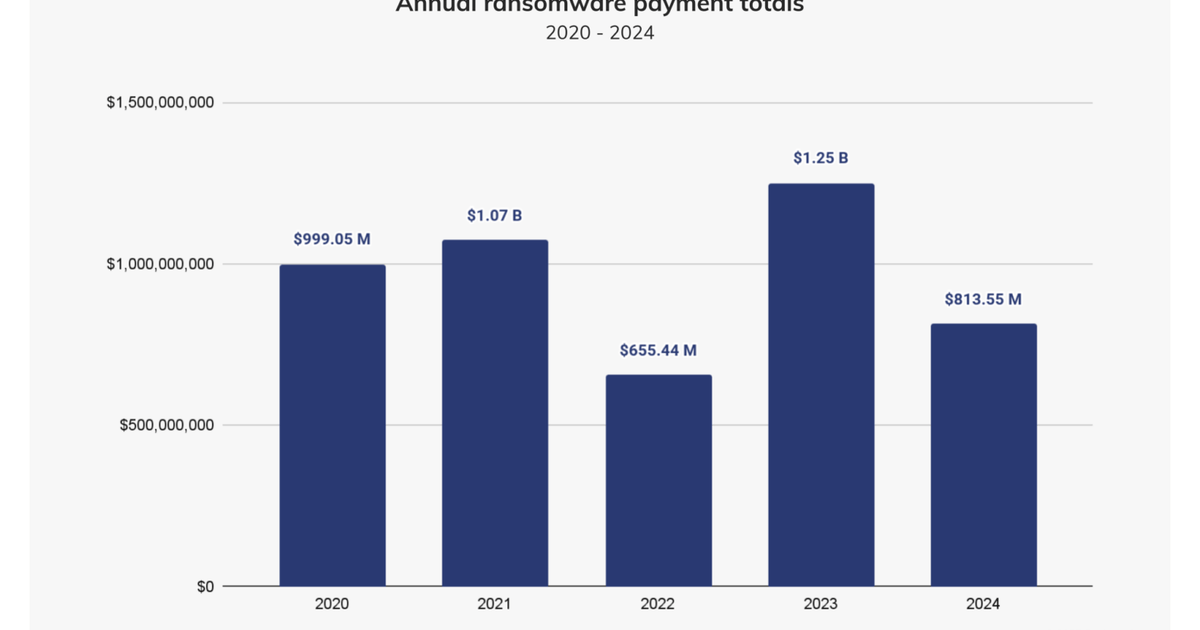
In 2024, ransomware attackers managed to collect around $813.55 million in payments, a notable decline from the $1.25 billion collected in 2023 and $1.07 billion in 2021, as outlined in Chainalysis’ 2025 Crypto Crime Report. Despite a slight increase of approximately 2% in payments during the first half of 2024, the overall year was projected to surpass the previous year’s totals. However, although the number of ransomware incidents saw a rise in the latter half of 2024, on-chain payments actually decreased. This trend suggests that although more victims were targeted, fewer succumbed to paying the ransom. In instances where payments were made, some victims were able to negotiate substantially lower ransom amounts.
Organizations that fall victim to ransomware attacks have long grappled with the moral dilemma of whether to pay or not. While paying may sometimes be the only way to swiftly recover crucial data or minimize downtime, it also inadvertently fuels criminal activities and potentially invites further attacks. Improved cybersecurity practices and enhanced resilience have empowered organizations to opt against paying the ransom, according to Christian Geyer, the founder and CEO of Actfore. The availability of better incident response capabilities, digital forensics, and data mining services has expedited the process of identifying breached data for victims.
Geyer noted, “Organizations have increasingly implemented comprehensive data backup solutions, enabling them to restore their systems rapidly through a wipe and restore process.”
Another significant factor contributing to the decline in ransom payments is the impact of law enforcement actions on the ransomware landscape. Several prominent ransomware groups that were active in 2023 and the first half of 2024 experienced decreased activity in the latter part of the year. One notable case is LockBit, which faced concerted efforts by law enforcement agencies from the UK, US, Canada, Japan, and Australia in Operation Cronos to seize data and websites associated with the group in February 2024. This coordinated disruption saw payments to LockBit criminals plummet by 79% in the second half of the year. Similarly, the disappearance of ALPHV/BlackCat in March 2024, after reportedly collecting $22 million from Change Healthcare, created a void in the ransomware landscape in the subsequent months, as highlighted by Chainalysis.
When a major player exits the cybercrime scene, either due to enforcement actions or voluntary cessation of operations, there is typically a temporary lull in activity before another group steps in to fill the vacuum. Surprisingly, this did not occur in 2024, according to Lizzie Cookson, a senior director of incident response at Coveware, in conversation with Chainalysis. Cookson remarked, “We saw a rise in lone actors, but we did not see any group(s) swiftly absorb their market share…The current ransomware ecosystem is infused with a lot of newcomers who tend to focus efforts on the small- to mid-size markets, which in turn are associated with more modest ransom demands.”
Overall, the evolving landscape of ransomware attacks and the various factors influencing victim decisions on payment underscore the complex interplay between cybersecurity, law enforcement actions, and criminal activities in the digital realm. As organizations continue to bolster their defenses and resilience against such threats, the dynamics of ransomware attacks are expected to undergo further transformations in the future.