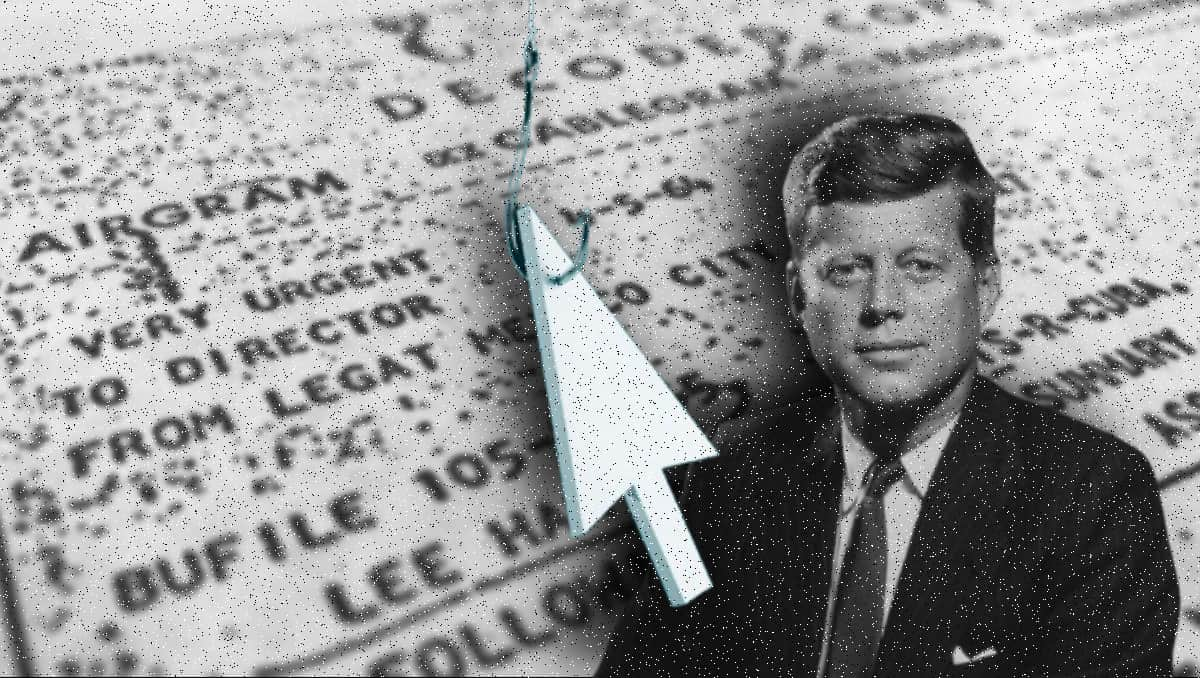
Veriti Research, a cybersecurity research firm, has uncovered a concerning cyber threat campaign centered around the release of declassified files related to JFK (John F. Kennedy), RFK (Robert F. Kennedy Jr.), and MLK (Martin Luther King Jr.). According to their findings, cybercriminals are taking advantage of the public’s interest in these historical documents to carry out various malicious activities like malware distribution, phishing scams, and exploiting vulnerabilities. The surge in media attention following the file release announcement has led to the rapid creation of potentially harmful online infrastructure.
Following the announcement of the file release, a number of suspicious domain names were registered, bearing resemblance to legitimate sources associated with the JFK files. Some of these suspicious domains identified by the Veriti Research team include “hejfkfilescom,” “jfk-filescom,” “rfkfilescom,” and “jfk-filesorg.” The timing and naming of these domains suggest that they could be used for phishing attacks, malware delivery, or social engineering tactics aimed at stealing user credentials.
Veriti Research outlined several potential attack vectors based on their investigation. These include embedding malware within files posing as official JFK document releases, creating fake websites that mimic government or media sources to deceive users into downloading harmful files, exploiting browser vulnerabilities through malicious websites, and conducting email phishing campaigns that impersonate reputable institutions or individuals offering exclusive access to the files.
This pattern of cybercriminal activity aligns with previous reports from Hackread.com, which have highlighted how malicious actors exploit major public events for their nefarious schemes. From COVID-19 scams to the Gaza crisis and California wildfires, cybercriminals have consistently capitalized on global events to further their malicious activities. Additionally, last year, Check Point Research reported on cybercriminals using Deepfake technology to manipulate voters and undermine electoral integrity, demonstrating their ability to adapt quickly to real-world events.
These incidents underscore the importance of maintaining cyber resilience against social engineering tactics. Attackers often leverage people’s curiosity and sense of urgency to lower their guard and carry out their malicious agendas. Veriti Research emphasized the necessity of verifying information sources and accessing declassified files only through official channels like the National Archives to mitigate the risks posed by this cyber threat campaign.
In conclusion, staying vigilant and cautious while navigating online platforms is crucial in safeguarding personal and sensitive information from cyber threats. By remaining informed, verifying sources, and adopting cybersecurity best practices, individuals can protect themselves from falling victim to cybercriminal tactics such as those targeting the JFK, RFK, and MLK file releases.