The latest cybersecurity disclosure regulations rolled out by the US Securities and Exchange Commission (SEC) have prompted a noticeable surge in incident reports from public companies. However, a substantial portion of these reports fail to encompass the material impact of said incidents, according to insights provided by a law firm specializing in finance and M&A activities.
Paul Hastings LLP’s analysis uncovered a significant 60% uptick in cybersecurity incident reports post the implementation of the disclosure rule in 2023. Under this SEC regulation, public companies are mandated to divulge material cybersecurity incidents within four business days of ascertaining their significance. The determination of materiality revolves around assessing the immediate repercussions and any enduring effects on a company’s functions, customer associations, financial standings, brand perception, and the likelihood of litigation or regulatory measures being taken.
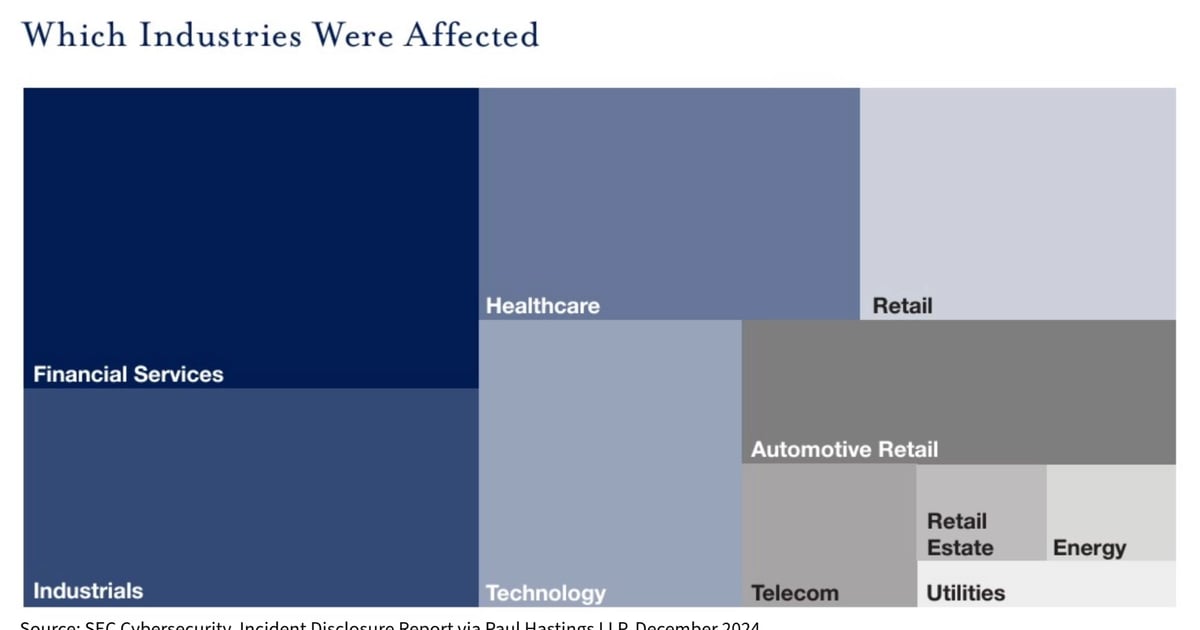
As depicted in the data chart above, the regulatory impact is widespread across various industries. While the financial services domain clocked the highest count of disclosure reports, industrials and healthcare sectors weren’t far behind. Both automotive retail and conventional retail entities found themselves grappling with cyber intrusions that necessitated reporting.
It is concerning to note that less than 10% of these disclosures elaborated on the material impacts of the incidents, hinting at the struggles companies face in striking a balance between comprehensive reporting and safeguarding internal operational specifics. The report cited instances of material impacts, such as Basset Furniture Industries alluding to a significant dent in business operations until recovery operations are finalized or First American Financial revising the earnings per share figures for the fourth quarter financial outcomes while quantifying the company’s losses in its SEC filings.
Interestingly, around 13% of companies opted to furnish a press release or refer to a blog post as a means to offer further insights into the incidents at hand.
The report sheds light on a critical aspect – one in four incidents were attributed to third-party breaches. Companies find themselves at a crossroads in deciding whether to disclose such breaches, particularly when other affected parties have already disclosed the incidents. The automotive retail segment bore the brunt of a ransomware attack on automotive software provider CDK Global in June. Subsequently, the parent company Brookfield Business Partners stated in its July disclosure that they did not anticipate a material impact from the incident. Contrarily, many smaller automotive entities reported a material impact due to CDK’s predicament.
The SEC’s recent enforcement settlements with four SolarWinds customers underscore the consequences of failing to provide accurate disclosures about the impact of cyberattacks. While two of the entities acknowledged the incidents publicly, they failed to disclose all pertinent details known at the time, such as the threat actor’s identity, nature of data breached, and the count of accounts compromised. The remaining two entities refrained from disclosing the incidents altogether, prompting the SEC to assert that they should have disclosed the impact.
Another intriguing aspect highlighted in the report is the dilemma between speed and comprehensiveness in disclosures. A significant majority (78%) of disclosures were made within eight days of uncovering the incident, with a third (32%) opting to file within four days. This rush to report can be attributed to companies’ desire to avoid penalties for delayed disclosure. However, the haste might hinder a thorough assessment of the incident’s ramifications, leading to 42% of companies issuing multiple reports for the same incident, each time furnishing additional details such as quantifiable losses, impact on customer data, and notifications to affected individuals and regulators.
In the wake of these findings, the report’s authors advocate for companies to continually assess their disclosure controls and engage in tabletop exercises to simulate the decision-making involved in determining materiality in the aftermath of a cyber incident. This proactive approach can better equip companies to navigate the intricate landscape of cybersecurity incident disclosures while maintaining transparency and accountability.
In conclusion, the surge in cybersecurity incident reports post the SEC’s new disclosure regulations underscores the evolving landscape of cybersecurity governance in the corporate sphere. The challenges faced by companies in balancing detailed disclosure with operational confidentiality serve as a poignant reminder of the imperative to fortify cybersecurity protocols and crisis response mechanisms in an increasingly digitized business environment. The onus now lies on companies to adapt, fortify their cybersecurity postures, and foster a culture of transparency and resilience in the face of mounting cyber threats.