In recent years, the threat to operational technology (OT) has often been overlooked amid high-profile data breaches and ransomware attacks on IT systems. However, attacking systems that interact with the physical world can lead to potentially devastating kinetic outcomes. A prime example of this is Ukraine, which has experienced disruptive attacks such as BlackEnergy and Industroyer, resulting in sabotage to its vital energy infrastructure.
The BlackEnergy attack in 2015 caused Ukraine’s first-ever blackout from a cyberattack, while the subsequent Industroyer attack led to mass power outages for Kyiv residents in the following year. In 2022, ESET researchers, alongside CERT-UA, revealed a new variant of Industroyer that aimed to cut power to a region in Ukraine. Fortunately, the attack was thwarted in time. These rare incidents emphasize that organizations, particularly those in critical infrastructure, cannot ignore the threat posed to OT systems.
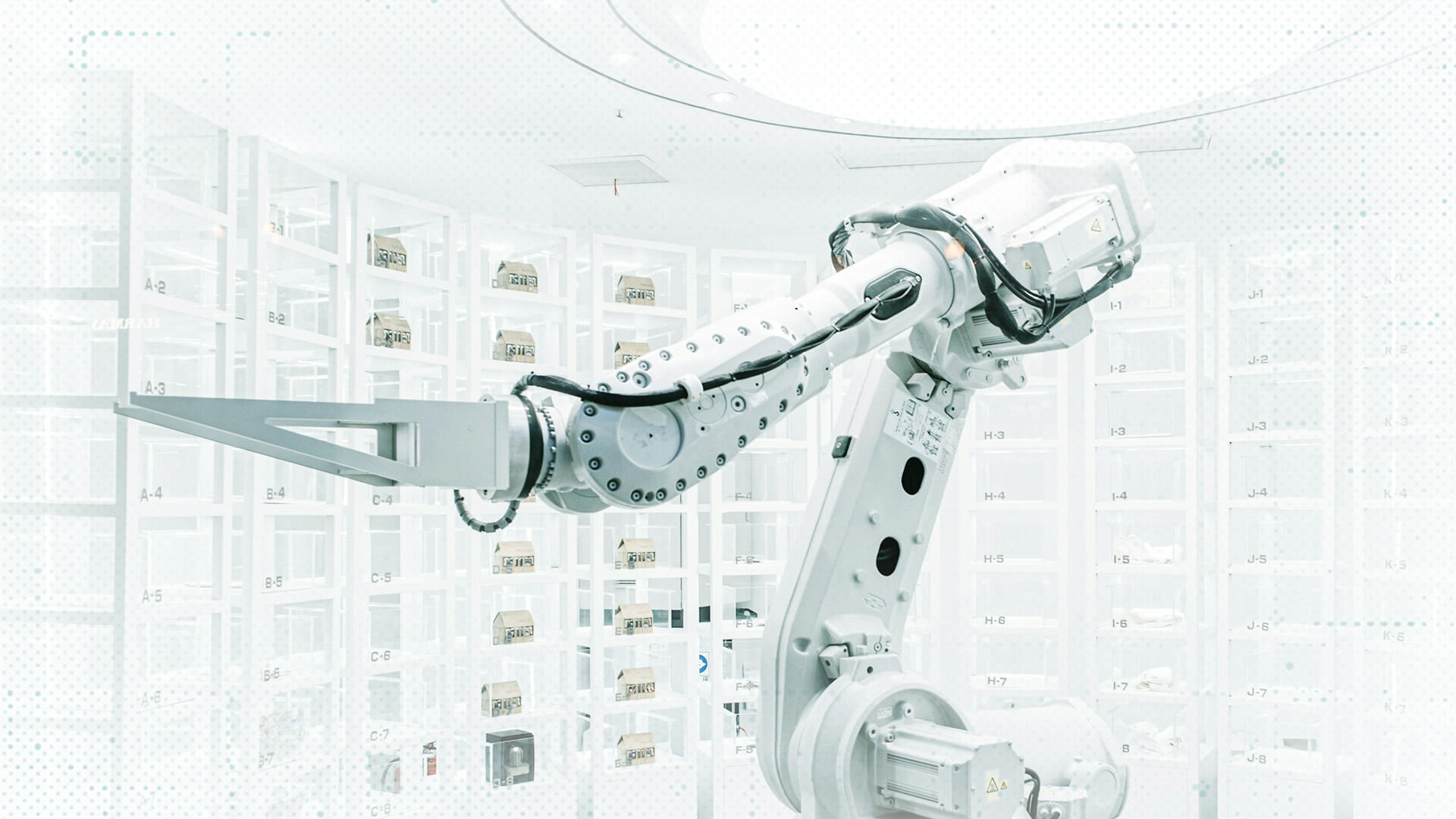
Unlike IT systems which manage information and applications, OT encompasses the hardware and software utilized to control physical systems in factories, industrial facilities, and various other sectors. The integration of internet connectivity into once isolated systems has left OT vulnerable to global threats, eroding the notion of “security through obscurity.” Additionally, the prevalence of Windows in SCADA and other OT environments, as well as standardized components, has made OT systems more susceptible to cyberattacks.
The impact of such attacks can be severe, including the destruction of critical infrastructure and disruption of business operations. According to estimates, there were 68 cyberattacks in the previous year that disrupted over 500 physical operations, marking a 16% annual increase. The cost per incident of serious attacks can reach up to US$140 million, excluding potential regulatory scrutiny in regions like the UK and EU.
OT security faces numerous challenges, including legacy insecure communication protocols, long hardware lifespans causing compatibility issues, and discrepancies in cybersecurity priorities between OT and IT teams. Additionally, the presence of legacy equipment that does not align with modern cybersecurity controls, insecure passwords, and misconfigurations pose significant risks to OT systems.
Mitigating risks to OT systems requires a multi-layered approach focusing on asset discovery and management, continuous vulnerability and patch management, network segmentation, identity and access management, threat prevention, data protection, supply chain monitoring, and people-first security. As threat actors continue to evolve, it is crucial for organizations to prioritize OT security and implement robust cybersecurity measures to safeguard critical infrastructure and prevent potential kinetic consequences.