In 2018, the Spectre and Meltdown vulnerabilities shed light on the susceptibility of computer memory to malicious attacks, prompting the tech industry to refocus on securing memory through innovative solutions. One of the key responses to this security crisis came from Microsoft, which ramped up its efforts to fortify the memory protection in its Windows systems.
Buffer overflows, a common avenue for hackers to infiltrate a system’s memory and execute malicious code, have been a major target of Microsoft’s memory security initiatives. To address vulnerabilities caused by the use of C++, a language notorious for its lack of memory safety, Microsoft is making a significant shift towards Rust programming language. Rust is being integrated into many system applications as a measure to mitigate memory-safety issues and prevent buffer overflows that put data at risk.
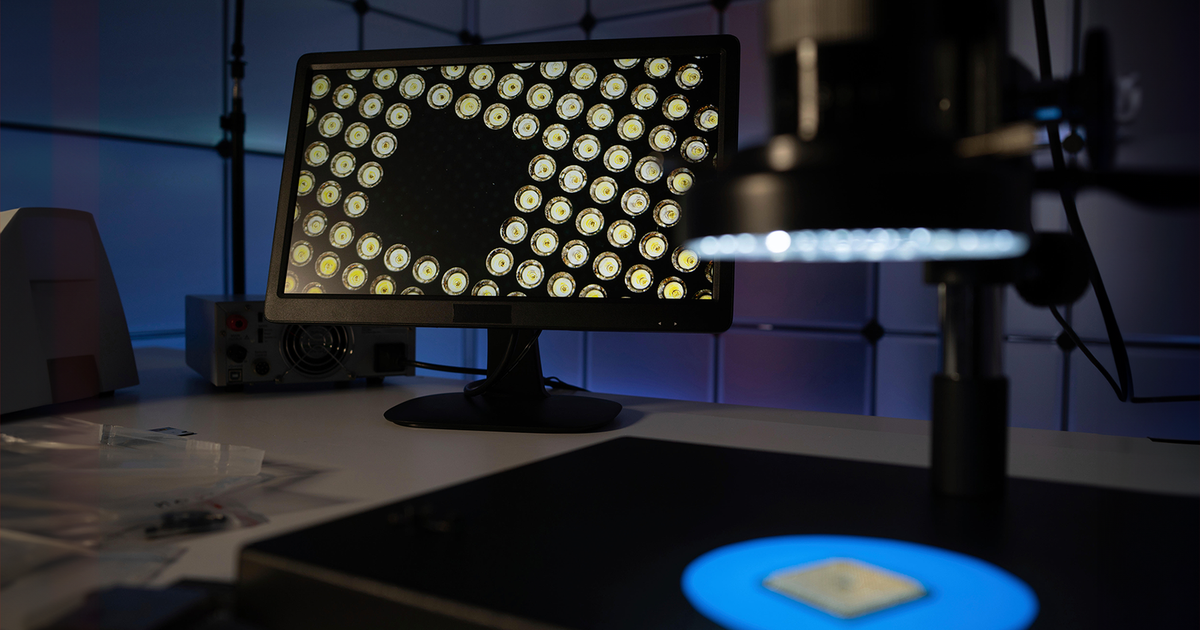
Furthermore, a coalition of chip makers came together in June to form the CHERI Alliance, dedicated to developing a secure hardware architecture that safeguards data stored in memory. This concerted effort underscores the industry-wide recognition of the urgent need to enhance memory security in the face of evolving cyber threats.
James Sanders, an analyst at TechInsights, emphasized the importance of memory-safe architectures and programming languages in averting human errors that could compromise system security. The prevalence of memory safety-related bugs in Microsoft’s software highlights the critical role of adopting robust memory protection measures.
Dave Weston, vice president of enterprise and OS security at Microsoft, disclosed the company’s strategic shift towards implementing Rust in system firmware and software management, marking the initiation of the Secure Future Initiative. This endeavor aims to consolidate Microsoft’s commitment to ensuring the reliability and safety of hardware through innovative solutions like incorporating security chips such as Pluton in new AI-powered PCs.
The CHERI Alliance’s mission to mitigate memory-related risks by introducing a comprehensive protection model for memory has drawn attention from industry experts. By enforcing a memory audit layer that verifies data access at every instance, the alliance aims to bolster memory security and combat prevalent threats posed by memory errors and hacks.
A researcher at the University of Cambridge, Franz Fuchs, highlighted the significance of encoding data in memory access to enhance security measures. The adoption of memory-safe chip architectures and operating systems derived from the CHERI designs showcases a proactive approach towards fortifying memory protection.
Despite the advancements in memory security, challenges persist, such as developer reluctance to embrace new security-centric mindsets, as noted by experts. The enduring threat of side-channel attacks on CPUs and GPUs underscores the need for sustained vigilance in safeguarding memory integrity.
Daniel Gruss, a professor in information security at Graz University of Technology, warned of the ongoing presence of memory safety bugs, even with the adoption of Rust in kernel development. As technology evolves, hackers continue to find loopholes in newer memory types, like GPUs, underscoring the necessity for ongoing innovation in memory security solutions.
In conclusion, the tech industry’s concerted efforts to bolster memory security in the aftermath of the Spectre and Meltdown vulnerabilities reflect a proactive response to evolving cyber threats. Through collaborative initiatives like the CHERI Alliance and strategic transitions to memory-safe programming languages, the industry is paving the way for a more secure computing environment.