Title: UNC1069 Targets Professionals with Fake Microsoft Teams Domains: A Rising Cyber Threat
Recently, cybersecurity experts have identified a troubling trend in the realm of cybercrime, particularly concerning threat actors associated with North Korea. This group, known as UNC1069, has been employing fake Microsoft Teams domains to engage in social engineering attacks and distribute malicious software. This tactic highlights the evolving nature of cyber threats, necessitating heightened vigilance among professionals and organizations alike.
UNC1069 has garnered attention for effectively manipulating trust and credibility, traits significant in their social engineering ploys. Financed by the Democratic People’s Republic of Korea (DPRK), this actor has a clear monetary motive underpinning their operations. Their recent activities include deploying a newly identified malicious domain, onlivemeet[.]com, which came to light on April 6, 2026. This fraudulent domain is designed to impersonate Microsoft Teams and host counterfeit meeting pages that lure users into downloading harmful software, namely a Remote Access Trojan (RAT).
The sophistication of UNC1069’s strategies is particularly alarming. They utilize methods that revive old conversations from past compromises, specifically targeting accounts on popular platforms like Telegram and LinkedIn. By resurrecting these conversations, they create an illusion of legitimacy that can easily deceive unsuspecting victims. Additionally, they are known to use social media platforms like Slack to impersonate legitimate company group chats, communicating fake partnership opportunities, investor calls, or job invitations to entice targets.
In a further effort to lend credibility to their schemes, UNC1069 has begun pre-scheduling these fraudulent meetings through legitimate services like Calendly. This tactic allows them to present themselves in a manner that appears both organized and professional, further lowering the defenses of potential victims.
The Mechanics of the Fake Meeting Lure
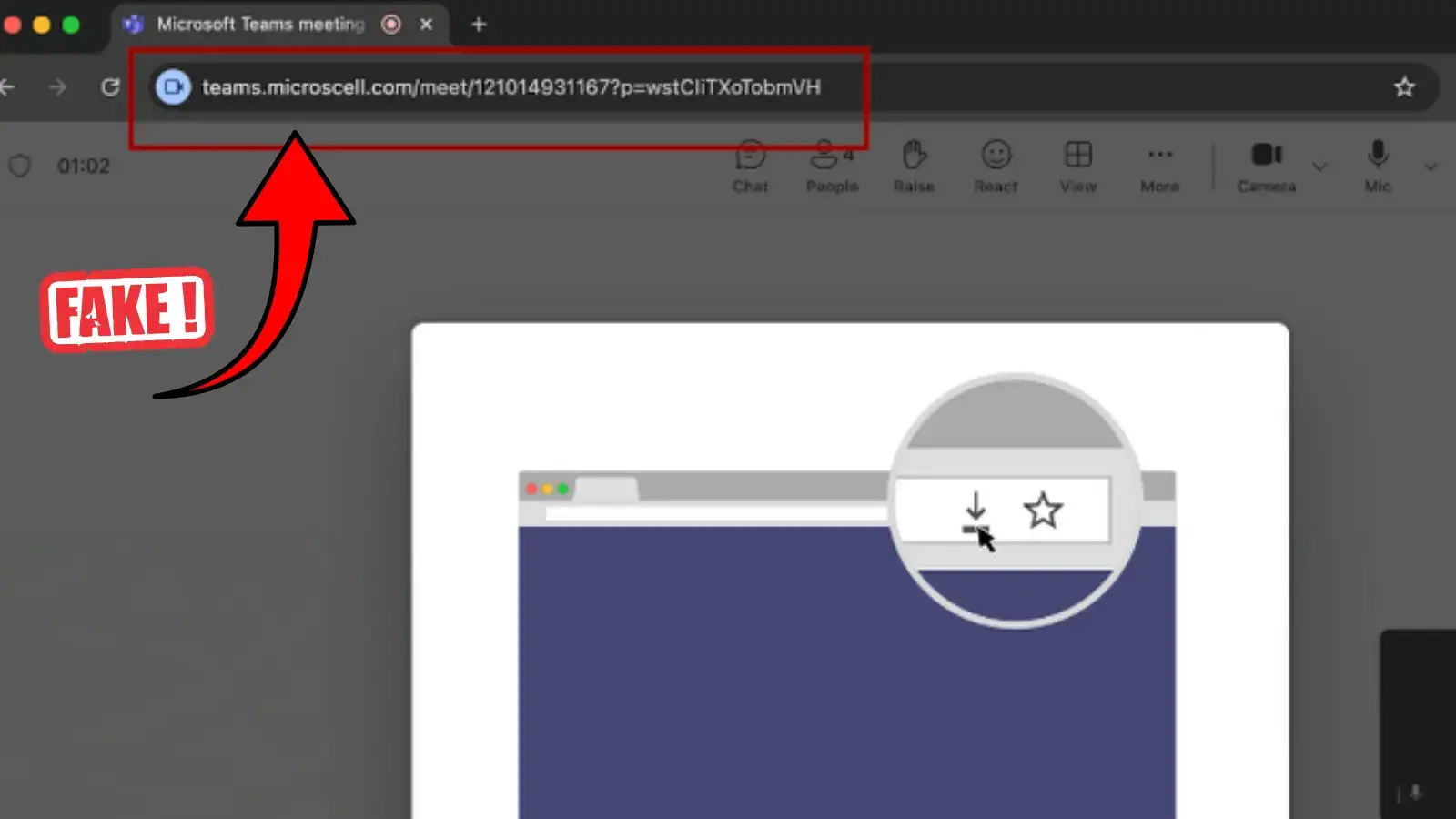
Once a victim engages with the fraudulent communication and clicks the provided meeting link, they are directed to a fraudulent Microsoft Teams webpage. This fake site is crafted with meticulous detail to mimic the appearance and functionalities of the real Microsoft interface, effectively disarming the victim’s suspicions. Once on this deceptive page, the user encounters a notice claiming that the "TeamsFx SDK" has been deprecated. It prompts the victim to click an "update" button that initiates the download of a malicious payload disguised as a necessary technical software fix.
This malicious payload is typically a RAT, which grants the attackers remote access to the victim’s computer system. Once installed, this software can harvest sensitive information, monitor user activity, and further propagate the attack on associated networks.
Defensive Measures Against UNC1069’s Tactics
As the threat landscape continues to evolve, organizations and individual users must remain vigilant in the face of such sophisticated cyber threats. Cybersecurity professionals advocate for a multi-faceted approach to defense against these attacks.
First and foremost, users are urged to scrutinize the actual URLs of links before clicking. In applications such as Slack and Telegram, what is displayed as a hyperlink may not accurately reflect the true destination. Organizations should also place significant emphasis on addressing unexpected meeting requests, especially those requesting immediate action, such as software updates, even if they appear to come from known contacts.
Ongoing training and education on cybersecurity best practices can empower employees to recognize and avoid falling victim to such attacks. Regular updates on current phishing methods and potential threats should be integral to organizational training programs.
Moreover, companies must invest in robust security solutions capable of detecting anomalies in network traffic and communication patterns that may indicate an intrusion. Firewalls, intrusion detection systems, and advanced endpoint protections are becoming increasingly essential in preemptively thwarting these kinds of cyber threats.
In summary, the activities of UNC1069 serve as a stark reminder of the persistent and evolving nature of cyber threats. Their methodical approach to social engineering, particularly through fake Microsoft Teams domains, raises significant concerns about security vulnerabilities in both professional environments and individual accounts. It is imperative that organizations and users remain vigilant, adopting proactive measures to defend against these ever-present threats. By fostering a culture of cybersecurity awareness, they can mitigate risks and safeguard their information and systems from malicious actors.