Cybersecurity researchers have been active in identifying the latest in cyber threats. One of the recent concerns has been the sale of AnyDesk accounts on Russian language dark web forums. AnyDesk, a popular remote desktop application, disclosed a security breach incident on February 2, 2024, involving unauthorized access to its production systems by unknown hackers. However, what’s concerning now is that cybersecurity researchers at Resecurity have disclosed alarming findings regarding the sale of compromised AnyDesk login credentials on both the clear web and the dark web.
This revelation is a game-changer and could potentially have dire consequences for individual users and enterprises. It’s crucial to note that the sale of AnyDesk credentials on the dark web is separate from the recent security breach. The stolen login credentials being sold are a result of infostealing malware infecting PCs to harvest sensitive information.
These findings come on the heels of a similar incident in June 2023, where hackers were found selling 100,000 ChatGPT login accounts obtained through devices infected with Raccoon, Vidar, and Redline malware worldwide.
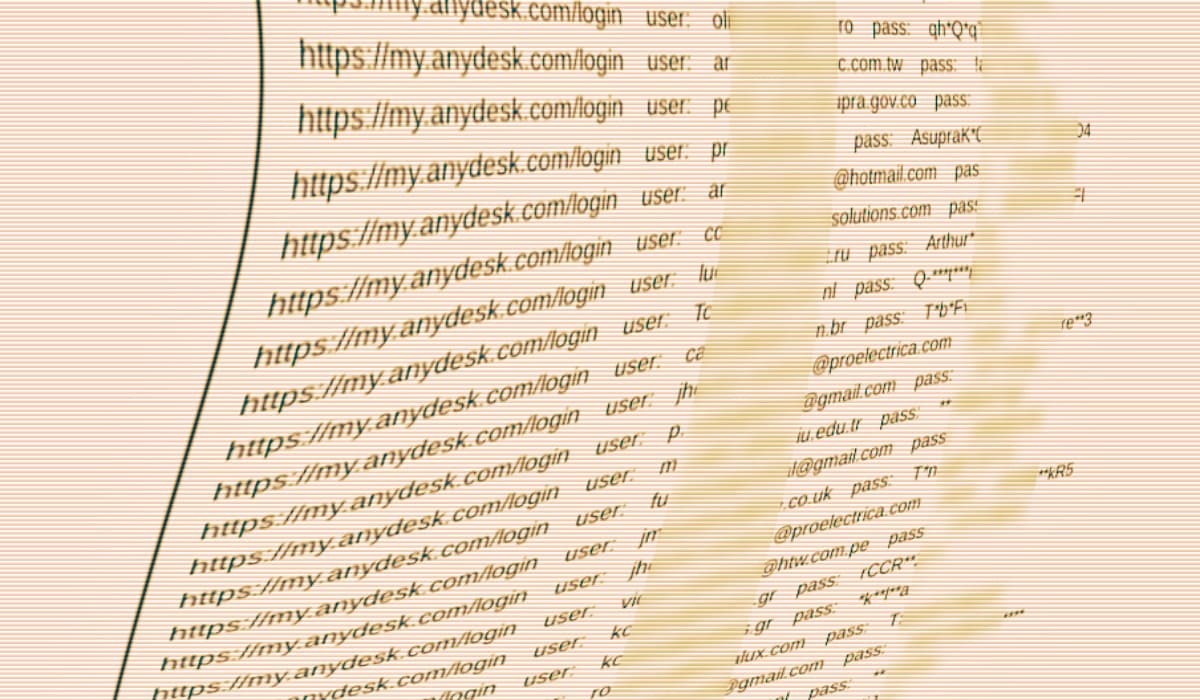
Resecurity’s blog post identified a threat actor operating under the alias “Jobaaaaa,” who has been observed selling 18,317 compromised AnyDesk accounts. These accounts are being offered for sale for $15,000 worth of Bitcoin (BTC) or Monero (XMR) cryptocurrency, with transactions facilitated through escrow services. These compromised AnyDesk accounts are being marketed on Exploitin, a cybercrime and hacker forum accessible on both the clear and dark web and primarily operating in Russian. Despite varying accounts of the number of credentials being sold, experts agree that the use of Escrow—a trusted third-party payment service—by the hacker adds a level of credibility to the offer.
Alon Gal of Hudson Rock expressed concerns and suggested the number of accounts being sold was even higher, with over 30,000 AnyDesk accounts up for grabs. This difference in numbers, however, doesn’t discount the very real threat that compromised accounts pose to unsuspecting users and organizations. The potential impact, whether on an individual or enterprise, would be devastating. The sale of these compromised accounts holds the potential for financial loss, identity theft, reputational damage, and operational disruption.
Resecurity’s latest revelation also shed light on the timestamps related to the sale of compromised accounts. The timestamps visible on the shared screenshots illustrate instances of successful unauthorized access on February 3, 2024, after the disclosure of the security incident. This alarming fact puts the gravity of the situation into perspective – hackers were able to successfully access and sell the compromised accounts even after the security breach had been made known.
Both individual users and enterprises must take immediate action to protect themselves. Changing passwords, being cautious of phishing emails, reporting suspicious activity, using strong passwords, enabling two-factor authentication, and staying informed about the latest security threats and best practices are some of the crucial steps that can be taken to mitigate the risk and protect against potential damage.
The sale of compromised AnyDesk login credentials is a stark reminder of the persistent and evolving cyber threats faced by users and organizations worldwide. It’s crucial to remain vigilant and proactive in safeguarding personal and sensitive information, especially in the wake of such concerning incidents.

